
CONTENT MANAGEMENT SYSTEM
Telling The Army Story
LOCALLY • NATIONALLY • GLOBALLY
What is CRE?
CORE is the Army's official content management system that provides the tools you need to build a digital presence for your organization.
- Publish articles
- Upload images & documents
- Create an organization web page
How can CRE? help you?
Get Organized
Manage your team more effectively with user roles, allowing supervisors to edit and approve content.
Get Published
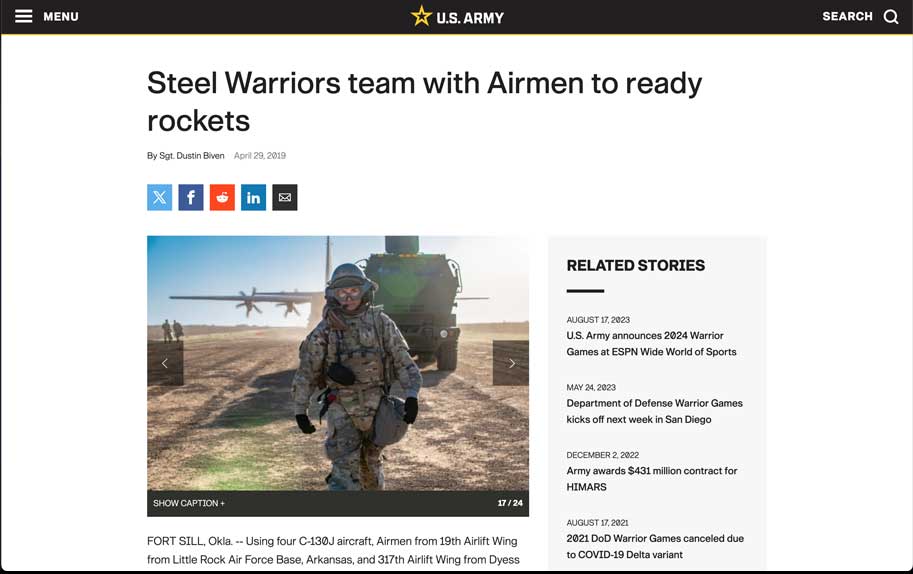
Your articles will be published to Army.mil, branding them on a platform that receives millions of views each month.
Get Featured
CORE articles are considered for the Army's homepage and official social media platforms, engaging a global audience.
Control Your Content
Organization pages display your articles, videos and other unit related information and resources.

Articles can be featured on the official army.mil homepage, growing your audience.
Article pages disseminate news and information, providing a permanent, long-form online presence linkable from social media platforms.
More Features. More Control. More Power.
Text Editor
Format text styles, including bold, italic, lists and hyperlinks.
Inline Images & Videos
Drag and drop media assets within the body of your article.
Embedded Videos
Integrate your organization's YouTube videos into your articles.
Schedule Releases
Schedule article to automatically release at a specific time in the future.
Tags
Categorize your articles with keywords, enabling users to explore similar content.
Team Management
Administrators control all team management and member settings.
Organization Page Management
Publishers can customize page settings, navigation and content sections.
Performance Metrics
Track content performance using Google Analytics.
Frequently Asked Questions
Am I eligible for a CORE account?
Any 46Q/46R/46Z or 46A Soldier, 1035- or 1082-series DA civilian or contractor serving in a public affairs capacity, is eligible. From basic contributors to administrators, we have a role for every public affairs professional. Learn more about eligibility
What is a CORE Page?
CORE Pages are organizational news sites hosted on Army.mil that serve as a public-facing tool to share stories, leadership information, and helpful resources with your audience. To qualify, your organization must be a two-star command or higher, or an installation newspaper. Learn more about CORE Pages
Do I need to have release authority to use CORE?
No, as a contributor you can create and submit articles for review by an editor within your organization. Once approved, users with release authority can publicly release them to Army.mil. Learn more about roles and permissions
What is EAMS-A and how do I use it to log in to CORE?
Enterprise Access Management Service-Army (EAMS-A) regulates access to secure Army sites by verifying a user’s identity and permissions. To log in, you use your CAC, selecting either the Authentication or PIV certificate. Learn more about CORE Login
What is required to release content to Army.mil?
To release content without additional review, you must be a public affairs professional who has graduated from the Defense Information School (DINFOS) or has a degree or equivalent professional experience in the fields of marketing, public relations or journalism; be OPSEC Level II trained; has been granted release authority by your command or organization; and is able to be the CORE Subject Matter Expert for your Org.
Where does my content go once submitted?
As a contributor, your content is sent to your organization’s editor inbox. Once released, your content will have a permanent URL on Army.mil and can be featured on the Army Homepage and CORE Pages. Learn more about submitting a draft
Can I import content from other platforms?
Yes. With a single-click import tool, content that your organization released on DVIDS can be pulled into CORE for publication on Army.mil. Learn more about DVIDS imports
How do I change my role within my organization?
Administrators are responsible for managing team member roles. You can find your administrator on the "My Organization" page within Community. Learn more about changing user roles
Still have questions?
Visit the CORE Support website to get more details about CORE features and in-depth training guides. You can also email the CORE Support Team with any questions.
YOU ARE ACCESSING A U.S. GOVERNMENT (USG) INFORMATION SYSTEM (IS) THAT IS PROVIDED FOR USG-AUTHORIZED USE ONLY.
By using this IS (which includes any device attached to this IS), you consent to the following conditions:
- The USG routinely intercepts and monitors communications on this IS for purposes including, but not limited to, penetration testing,COMSEC monitoring, network operations and defense, personnel misconduct (PM), law enforcement (LE), and counterintelligence (CI) investigations.
- At any time, the USG may inspect and seize data stored on this IS.
- Communications using, or data stored on, this IS are not private, are subject to routine monitoring, interception, and search, and may be disclosed or used for any USG-authorized purpose.
- This IS includes security measures (e.g., authentication and access controls) to protect USG interests--not for your personal benefit or privacy.
- Notwithstanding the above, using this IS does not constitute consent to PM, LE or CI investigative searching or monitoring of the content of privileged communications, or work product, related to personal representation or services by attorneys, psychotherapists, or clergy, and their assistants. Such communications and work product are private and confidential. See User Agreement for details.