What do you call a conference room filled with curious students, military cyber professionals and computers? A hackathon.
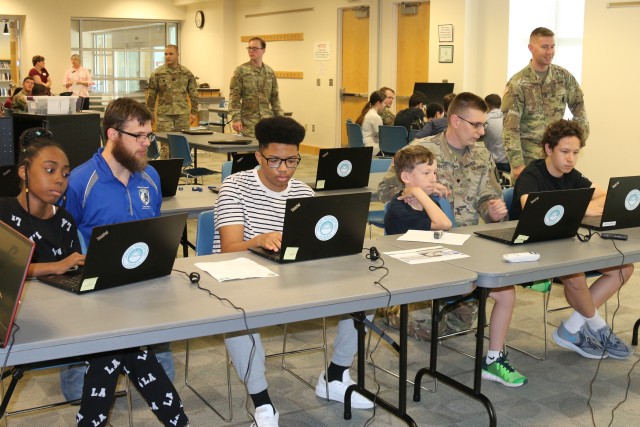
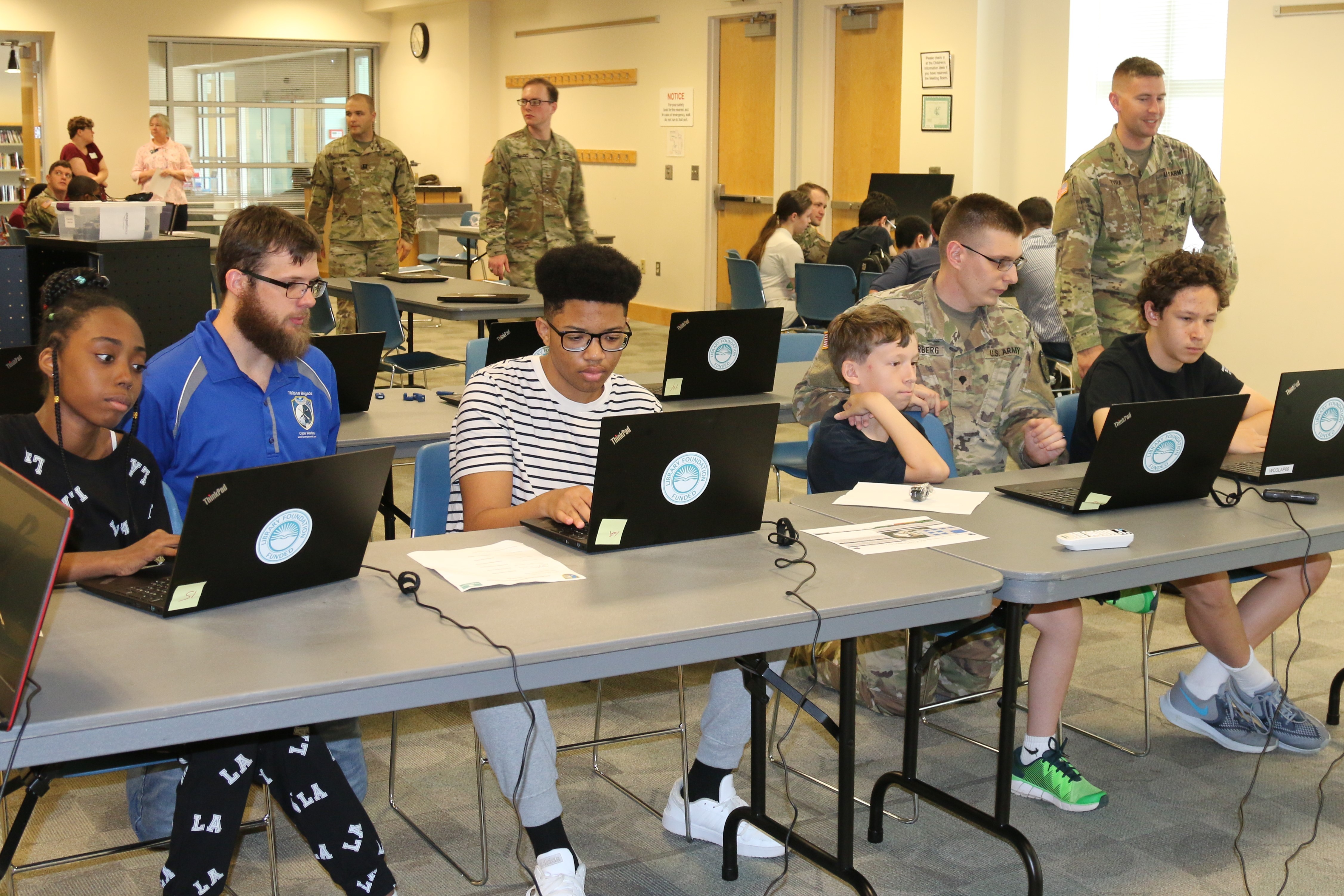
Soldiers of the 780th Military Intelligence Brigade (Cyber) hosted the free, educational hackathon on Sept. 10 at the Odenton Regional Library.
The hackathon is the first of three monthly programs in partnership with the Maryland STEM Festival at the library that celebrates teaching science, technology, engineering and mathematics. The library has been in partnership with the Maryland STEM Festival since 2015.
"STEM programs are part of our extensive educational offerings that serve babies to seniors," said Christine Feldman, communications specialist for the Anne Arundel County Public Library. "Our mission at the library system is to educate, enrich and inspire the residents of Anne Arundel County.
"STEM knowledge is vitally important for the future of our country. We regularly offer STEM programs for preschoolers, school-aged kids, teens and adults throughout the year, but give special focus during Maryland STEM Festival month."
The hackathon featured seven demonstrations with about 11 mentors providing instruction and guidance.
The hands-on learning session was organized by 2nd Lt. Alan Baily, 780th MI planning specialist, who provided instruction and supervised the station activities.
"A hackathon is a pretty ambiguous term," Baily said. "It's really hard to define. We decided to focus on some of the basic cyber security principles that a lot of hackers use -- whether that is password cracking, web server proxies or a myriad of different tools the students can use."
Baily outlined the process.
"First, start out with demonstrations and explain the ethics behind each," he said. "The intent is to show the students what is actually available and the [outcomes]."
Ultimately, a hackathon event is an opportunity to facilitate science, technology, engineering and mathematics teaching and experiences through guided computer simulation followed by replication.
The event also exposed students to procedures for safeguarding computer usage while introducing them to various fields of information technology.
Parents Encouraged
The 780th MI provides support to the Anne Arundel County Library as a way to enrich, expose and educate the community to STEM with recurring, free educational events.
Many parents were elated to have their children participate in the event.
"I found out about this event from the library for my son, Gabriel," said Jacqueline Till Graham, a retired master sergeant from the 902nd Military Intelligence S5 Logistics unit. "He attends Arundel Christian School. They do not have a [full] STEM curriculum, but they just started a computer programming class."
During the three-hour event that started at 4 p.m., students rotated from station to station.
One station, "Cracking the Perimeter," received lots of attention from the participants. Students learned how security is evolving in the cyber industry and moving away from past technologies.
The demonstrator explained how wireless networks in a home network for students can be unsafe and why modern wireless practices are moving to WPA2 as a more secure tool.
At the "Password Cracking" station, students learned the basics to hacking a password.
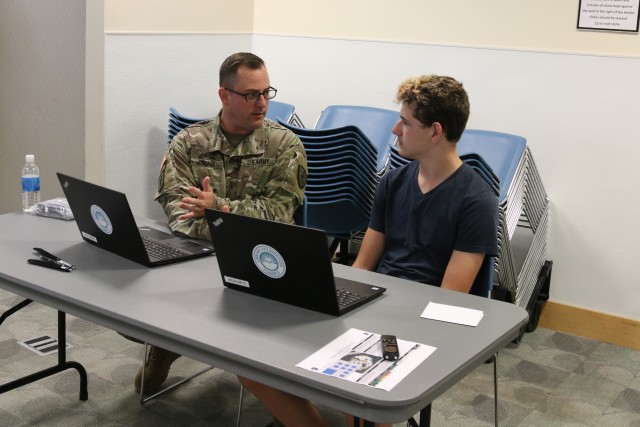
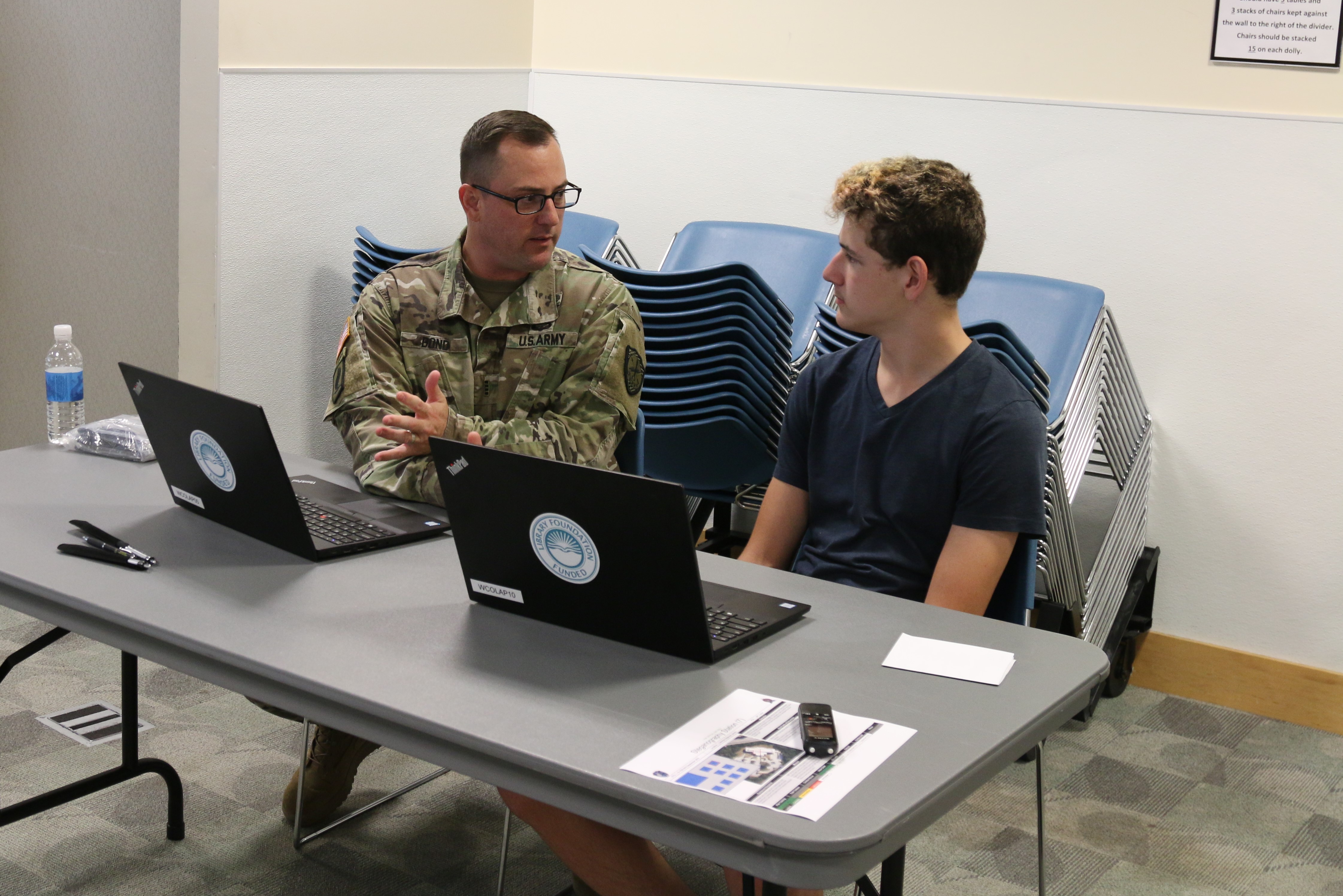
Chief Warrant Officer 4 James Richards of the 780th MI, who pursued an undergraduate degree in computer science prior to joining the Army's Signal Corps, outlined the importance of safeguarding passwords for websites, smartphones and internet connectivity.
"If you are trying to make a secure password, make it long," Richards said. "It does not need to be complicated. There's a website called 'How secure is my password?'
"You can use it at home to check how secure your password is."
Influencing Students
At the binary station, 2nd Lt. Rebecca Acheson of the 707th Communications Squadron displayed a simulation that resembles a video arcade game.
The game allows participants to learn how computers communicate through binary code, which included numbers and letters.
"[With] this binary game, you have different numbers: binary, hex and octal," Acheson said. "[Then] you have to try and make the number you see on the screen.
"If it is a binary number -- 1, 2, 4 or 8 -- you have to go to the right. And if you hold left, you use numbers 16, 32, 64 and 128."
Career opportunities within STEM fields are growing in demand. According to data from the Pew Research Center, since 1990 employment in STEM occupations has grown 79 percent, increasing from a workforce of 9.7 million to 17.3 million.
"Having the opportunity to influence students, whether they pursue a career in the Army, is not the goal," Baily said. "[The goal is] to get them excited about what we do."
Early exposure to STEM activities can lead students into pursuing STEM careers.
The Steganography station allowed students to decode messages that had been embedded through other files such as PDFs or photos.
Lyam Harbaugh, 15, a home-schooled student who runs a computer technology business, was enthusiastic about the hands-on activities.
"It's been a year now [that I've been] coding stuff," Lyam said. "My dad works in this field, so he's been teaching me about [computers] all my life."
Editor's note: The next hackathons are Oct. 8 and Nov. 12 from 4-7:30 p.m. at Odenton Regional Library. Register at https://www.aacpl.net/location/odenton.


Social Sharing