FORT HUACHUCA, Ariz. —Cybersecurity Engineers from the U.S. Army Information Systems Engineering Command, a major subordinate of the U.S. Army Communications-Electronics Command, have been working hand in hand with information system owners or ISOs from the U.S. Army Installation Management Command to utilize the new U.S. Army Risk Management Framework (RMF) Common Control Provider (CCP), known as the 'Army Sentinel.‘
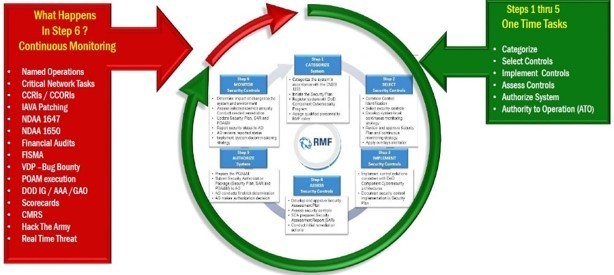
"Sentinel is the first step in meeting the Army objective on how it tackles RMF, which is to shift focus to readiness and continuous monitoring," said Melrone McCray, ISEC Mission Engineering Directorate (MED) cybersecurity engineer
The new CCP, developed by the U.S. Army Network Enterprise Technology Command (NETCOM) Cyber Security Directorate, Risk Management Division, seeks to "operationalize" cybersecurity by prioritizing RMF security controls into a more streamlined, threat-focused control set. The introduction of Project Sentinel is the first step towards accomplishing this endeavor.
"When the system ISO follows the Sentinel TTP closely for the new control provider inheritance, it will not only put the systems' control sets in a good place for new authorization, but in many cases, it will also minimize the number of controls that will need to be continuously monitored," said James Scott, MED cybersecurity engineer
Applying the Sentinel CCP overlay will replace the need to apply the currently used DoD tier 1 and Army tier 2 overlays.
“The overall intent is to ensure the mission can be accomplished while assessing operational risk,” said Deb Harvey, MED Group Leader. “By utilizing Project Sentinel, as well as properly configured overlays, an organization can determine what security controls are necessary and then spend their time focused on securing those controls.“

Social Sharing