BUTLERVILLE, Ind. -- Cyber warriors from the Army Cyber Protection Brigade (CPB) had an opportunity for realistic state-of-the-art cyber training at the Indiana National Guard's Muscatatuck Urban Training Center (MUTC) here, Aug. 20-24.
The cyber Soldiers, from the brigade's 154th and 155th Cyber Protection Teams (CPTs), 1st Cyber Protection Battalion, deployed to MUTC to conduct cyberspace operations in defense of a deep-water port city in the fictional nation of Sokovia, in the fourth iteration of a live, scenario-based situational training exercise (STX) dubbed Operation Tiger Stance (OTS).
OTS was supported by participants representing a broad swath of the Department of Defense Cyber Mission Force. In addition to the CPB and Indiana Guard, Army Cyber Command (ARCYBER); Marine Corps Forces Cyber; U.S. Air Forces Cyber; and the SysAdmin, Audit, Network and Security (SANS) Institute, a cyber defense research and training organization founded in 1989 to help train cyber defenders, took part in the exercise.
The OTS scenario for this iteration centered on an interactive battle against a cyber adversary attacking the Sokovian town, specifically its port and the facility's Industrial Control Systems (ICS).
The town -- the MUTC complex - is a facility built on the complexities of a modern city to provide training on complex terrain with a human signature, said Lt. Col. Chris Mabis, the MUTC commander.
Mabis described the center as a full-size replica of six blocks of a megacity that contains features such as an embassy, oil refinery, shanty town, school, farm, hospital, radio station, water treatment plant, subway and bus stations, housing, prison, and more. The facilities are real buildings with electricity, water and furnishings, where effects such as smoke, flames and water can be employed to add realism to training events. However, the actual port employed for this training iteration was a tabletop model built to mirror the networks and ICS of a full-size facility.
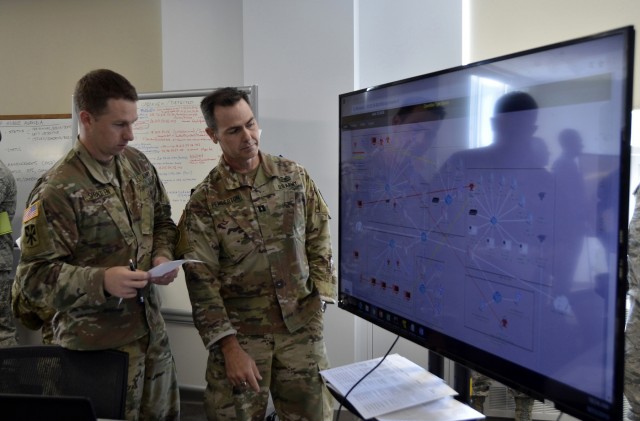
MUTC also functions as "Cybertropolis," an advanced urban cyber testing and training environment that boasts 70 structures wired with fiber optics to bolster exercises, Mabis said. These supported an array of cyberspace assets used during OTS to replicate those found in real cities -- city, base and port networks; Internet providers, social media networks, websites, retail stores, and random online traffic designed to mimic the "fog of war" in the cyber domain.
"The training that cyber operators execute here at Muscatatuck is a powerful replication of real-world operations and is closely tied with ARCYBER's exercises across the information environment and cyber-electromagnetic domain," said ARCYBER Deputy Commanding General (Operations), Brig. Gen. Rick Angle. "The convergence of cyber and kinetic operations in this complex training environment challenges, educates and strengthens the readiness of our Total Army cyber team."
MUTC, along with the Indiana Guard's training facilities at nearby Camp Atterbury, provides an extensive complex for multi-domain training.
"Atterbury-Muscatatuck is a platform that offers all services the ability to train in the air, land, sea, cyber and space domains to enhance readiness in preparation for a near-peer competitor battle," said Maj. Gen. Courtney P. Carr, The Adjutant General of Indiana. "MUTC offers the most realistic cyber environment in DoD for Cyber Support to Corps and Below."
The defender of the town -- the "blue team" -- was made up primarily of members of the 154th and 155th CPTs. Opposing them was a "red team" comprised of experts from SANS and additional CPT members. SANS and CPT personnel also enabled and facilitated exercise activities as an operations team and "white team."
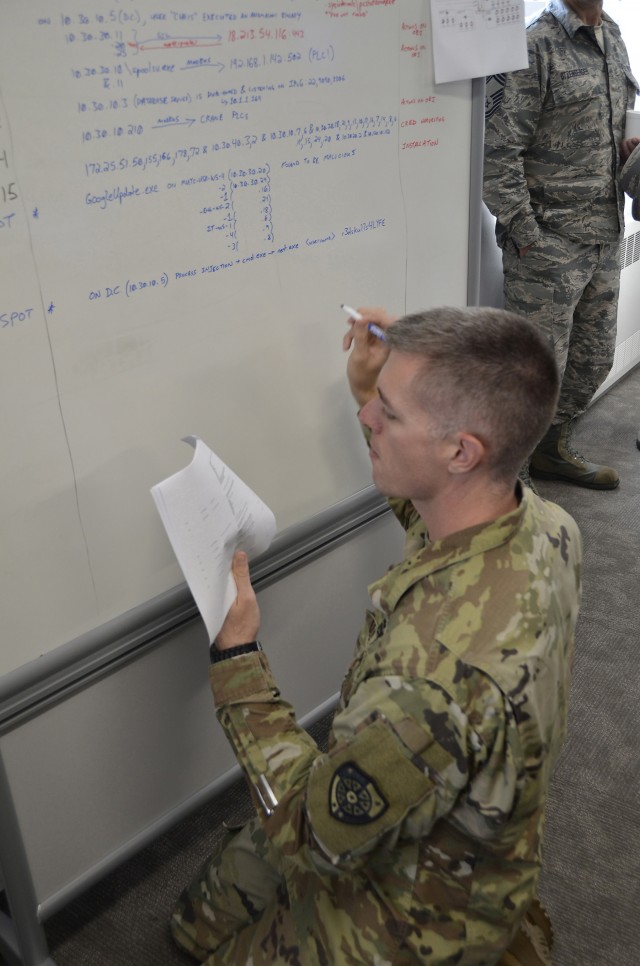
Red team actions were based on real-world activity and actual tactics and techniques used by nation-state actors, and allowed attackers to escalate their efforts and respond to events in real time based on blue team activity, explained SANS fellow Ed Skoudis. Defenders were challenged to use multiple tools to detect and counter a variety of attempted attacks and strategies to secure networks, establish or re-establish control of systems and services, restore lost and degraded services and enable local defenders. To meet those objectives they fought their way through an array of red team tactics such as antivirus evasion, network enumeration, ransomware, client-side attacks, pivoting, exploitation of network services, privilege escalation, domain attacks and attacks against ICS such as remotely seizing control of the port's cranes to disrupt operations.
The overall goal of OTS was to produce an exercise that not only prepares the CPTs for task force-oriented real-world operations, but also for deployment and troop movement, explained Maj. Joe Marty, 1st Cyber Protection Battalion director of operations. CPT members went to Hunter Army Airfield in Savannah, Ga., prior to OTS to practice preparing themselves, their movement plans and procedures, and their gear, for air mobile deployment. To kick off the exercise weeks later, they responded to a 3 a.m. alert and deployed to Indiana via commercial aircraft, ground transportation and finally, by helicopter into MUTC.
The CPTs had to identify and deploy with their own tools, along with their knowledge of operating systems; ICS skills; the ability to detect, research and attribute attackers; and the capability to stop them. Even so, the teams had to be prepared to request vital support (such as additional analysis assets) from elements back at home station, as well to integrate and coordinate staff actions, reporting and command and control as elements of a battalion task force, to successfully take on OTS.
Skoudis said the genesis of the STX can be found in Net Wars, a cyber range environment developed by SANS in 2009 for military and civilian training, and Cyber City, a miniature city created in the group's research facility in 2012 to "move our cyber range experience into the kinetic space." In 2014, he added, MUTC officials asked SANS to use its expertise to create a full-scale version of that model. The result was used to conduct an STX proof of concept in 2016, followed by training iterations with the CPB over the next two years.
While OTS was built within the SANS network and scenario, it also incorporated facets of exercises at the Army's Combat Training Centers, U.S. Cyber Command standards, and essential task force and battalion tasks and procedures to ensure the exercises provide individual and collective training in full-spectrum defensive and offensive cyberspace operations. SANS also worked closely with the CPB as they built training scenarios, to ensure the brigade's training objectives for dealing with real-world persistent threats would be met.
"We build the training scenario with certain learning objectives in mind," Skoudis said. "It operates with those learning objectives, then they (CPB) evaluate themselves to (determine), 'Did we learn what we were supposed to learn?'"
During the STX each CPT focused on separate aspects of key terrain on the training area network, explained CPB Information Services Technician Chief Warrant Officer 3 Michael Butler. The 154th CPT was responsible for the ICS/Supervisory Control And Data Acquisition (ICS/SCADA) segment while the 155th CPT's job was to defend enterprise services.
"Being able to have an enterprise network directly joined with an ICS network is very realistic if we were to respond to a state threat actor," said the CPB's Capt. Seth Hayden, who acted as the officer-in-charge of the exercise's white team.
Throughout operations, Butler said, the role of the task force was to remain operationally aware of what both teams were doing and provide mission command for multiple CPTs operating in close proximity and on the same network.
"The intent is provide the most realistic, real-world scenario in regards to troop movement, defensive cyber operations, and mission command," Marty said. "Current training exercises (such as brigade combat team rotations at the Army's Combat Training Centers) use Cyber Protection Teams as training aids. This exercise targets the CPTs as the training audience."
"Secondly, it is not the teams as a whole that participate (in CTC rotations); it is typically a mission element consisting of five to 10 cyber warriors. This exercise allows the CPTs and battalion to train together as a task force, just as they will operate in real-world missions."
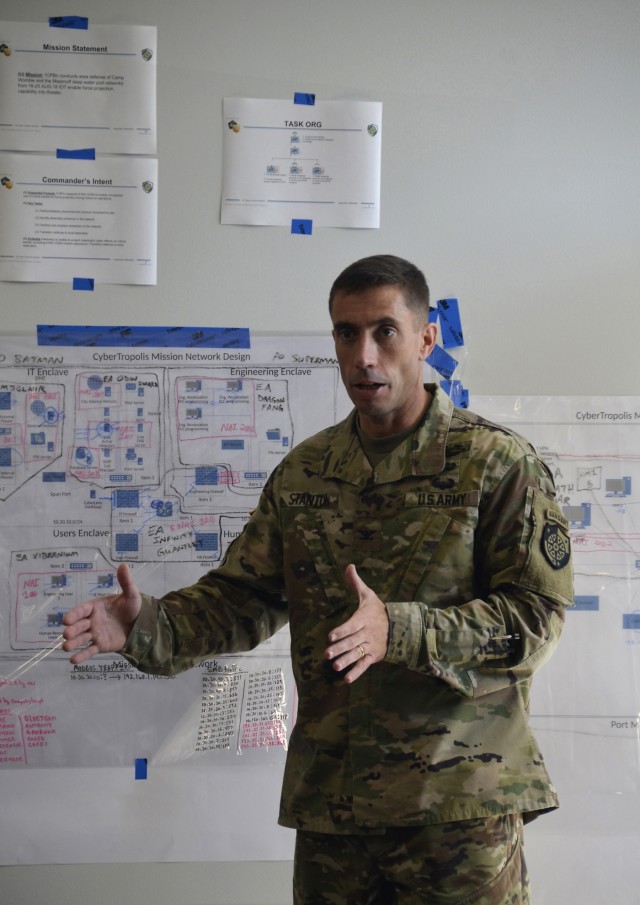
"These exercises are so important, because they give our Cyber Protection Teams an opportunity to focus on refining not just hands-on-keyboard cyber skills, but also how to operate as a battalion task force," said CPB commander Col. Paul Stanton. "The ability to seamlessly integrate and execute with the staff, and coordinate command and control functions is critical to the defense of our people, operations and vital warfighting systems in cyberspace."
While task force operations are vital to the brigade, Marty said they represent an area where the CPB has had little training or practice.
"The Cyber Protection Battalion was not built, manned, or trained to operate as a task force," he explained. "We evolved to operate this way out of necessity to meet the demands of the mission. ... This multi-CPT task force faces the challenge of exercising and improving processes that most are not trained nor experienced in executing. Most individuals and CPTs operate in smaller-scale environments with greater autonomy - additional support is only provided upon request and isn't timely. The teams are usually supported in their deployments through the force projection processes developed and executed by their parent battalion. (For OTS) the task force is the battalion, so we are responsible for mission command, intelligence support, and force projection."
The battalion battle staff focuses on building mission command processes and integrating team leadership into supporting them, while the CPTs focus on developing and exercising individual and team-level tactical and technical tasks. Assessors and observer/controllers from the CPB, as well as from National Guard, Marine Corps and Air Force CPTs, evaluated each level throughout the exercise.
Training alongside cyber professionals from the National Guard and other services and agencies allows the entire community to come together in a collective effort to share ideas and tactics, techniques and procedures, Butler said.
"Cyber is in a constant state of flux and we can only enhance our capabilities after bridging the gaps between active and reserve forces. At the end of the day, we all have the same goal in mind: to better defend the assets and interests of the United States," he said.
"The combination of a venue capable of replicating an enormous array of real-world cyberspace operations challenges and the talent that our National Guard partners bring to the fight from their cybersecurity careers with tech industry leaders gives the brigade an unbeatable training package," Stanton added. "Every time we train here those partnerships get stronger, the training gets more realistic and more challenging, and the value we derive from them grows exponentially."
For more information on the Indiana National Guard's Atterbury-Muscatatuck training complex, go to https://www.dvidshub.net/news/291592
-----
ABOUT US: United States Army Cyber Command directs and conducts integrated electronic warfare, information and cyberspace operations as authorized, or directed, to ensure freedom of action in and through cyberspace and the information environment, and to deny the same to our adversaries.
Interested in the challenge of joining the Army Cyber team? Check out military and civilian cyber career and employment opportunities by clicking on the "Careers" tab at www.arcyber.army.mil









Social Sharing