The information age has brought unique challenges and opportunities to logistics in war. Information management has taken center stage as data flows up and down the supply chain with incredible speed and volume. Military logisticians have enjoyed a vast array of new enterprise management tools that were not available just a few decades ago.
Despite these technological leaps, the uncertainty of the battlefield remains a constant factor in enterprise logistics. In the dynamic environment of war, logisticians need to understand the critical vulnerabilities of information age logistics. Today's logistics doctrine emphasizes the advantages of information age concepts and downplays their weaknesses. What modern doctrine seems to lack is deeper thinking about how the fog and friction of war could upset predicted outcomes for an information-based logistics enterprise. Predicted outcomes should account for both advantage and vulnerability.
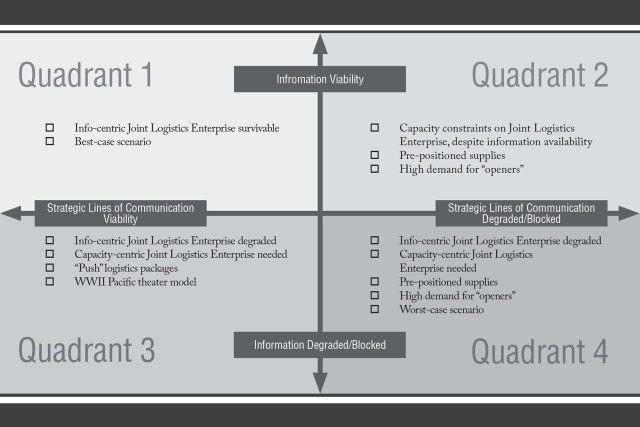
A framework of potential challenges in a contested environment shows that capacity-centric logistics concepts are still relevant to modern warfare and should remain part of logistics strategy.
FOG AND FRICTION
Unexpected disruptions caused by fog and friction are always major challenges for logisticians. For Carl von Clausewitz, friction was a defining aspect of war and included aspects of uncertainty that are now associated with the term "fog of war."
Fog, in keeping with popular understanding of the concept, refers to the ambiguous nature of information in war and the difficulties encountered in maximizing good information. According to Clausewitz, friction "is the force that makes the apparently easy so difficult." Friction is the interaction of chance and action and can be caused by many factors, including enemy forces, friendly actions, or the environment.
Most importantly, fog and friction cannot be erased from warfare regardless of advances in thinking and technology. Advances in technology change the nature of uncertainty, but they do not eliminate it. The biggest danger of the information-centric approach to logistics is the assumption that "good information" will be enough to peel back the fog of war and prevent unexpected disruptions. Unfortunately, warfare is far too unpredictable no matter how good the information process is.
I have developed a framework for thinking about the information challenges that the joint logistics enterprise (JLEnt) could face in a contested environment. (See figure 1.) The framework addresses the vulnerabilities of the JLEnt as they relate to information and the physical lines of communication (LOCs).
In this framework, the level of information viability or degradation refers to how well information flows. Does information move easily and effectively, or is it impeded by an adversary or even friendly actions? For the logistician, this is the level of friction encountered in the process of collecting good information.
The other axis of the framework is strategic LOC viability or degradation. It includes the physical infrastructure and components of the coalition. Seaports, sea lanes, air lanes, aerial ports, road networks, and other transportation assets are strategic LOCs. The viability of strategic LOCs, in both friendly and contested areas, is described on the horizontal axis.
The framework lays out basic characteristics of the environment that the JLEnt could face. At any point a conflict could shift from one scenario to the other in an unpredictable way. Multiple quadrants could be true simultaneously, although the unexpected disruptions caused by fog and friction will cause definite pressure toward certain outcomes, often negative.
The goal of this framework is to broaden thinking on potential outcomes for the JLEnt and contribute useful terms for discussing how logistics could be affected by the context. The practitioner should not take the framework as dogma but simply as a starting point for asking better questions.
QUADRANT 1
Quadrant 1 of the framework is the best-case scenario for the JLEnt. Much of Department of Defense doctrine envisions a future contested environment in which both information and LOCs, to and from the theater, will remain viable enough for supporting operations. Doctrine assumes a successful defense.
Quadrant 1 is a risky basis for scenario building, and it should not form the backbone of the planning process. Should events break in favor of a U.S. coalition, the JLEnt will be able to perform as envisioned, so little needs to be added here about a best-case outcome.
QUADRANT 2
The Quadrant 2 scenario aligns with predicated doctrinal outcomes in the information space because it assumes the networks will be protected and viable enough for operations. Computer networks and data systems will be adequately defended and information will flow as needed for command and control. Portions of the supply chain, however, could be degraded or closed by an audacious adversary.
In this scenario, the JLEnt will once again be forced to overcome physical limitations more than informational friction points. Despite intact information nodes, the degraded supply chain will be the defining theme of this scenario. Capacity-centric ideas, such as pre-positioned supplies, will play a sizable role if LOCs are not viable and reliable.
An adversary could attack the LOCs in many ways. Some techniques already available include autonomous torpedoes capable of traveling long distances to U.S. seaports and drones operating in swarms around key airfields. It is possible that even strategic nodes in the United States could be challenged with these techniques. This type of attack is becoming easier to carry out as technology proliferates for advanced adversaries.
The "openers," capabilities in the force that can be used to open new logistics nodes, will be invaluable tools for this type of scenario. An opener capability may require creative technological solutions for moving materiel. This includes ship-to-shore and shore-to-ship capabilities in the event that friendly ports are compromised.
The hastily deployed and strategically significant "Mulberry harbours" that the British developed during World War II are a good example of the type of opener capability that will be required in a contested environment. The joint task force-port opening (JTF-PO) is a more recent example. The JTF-PO would require major expansion if aspects of the contested environment fall into Quadrant 2.
Today's JTF-PO may not be robust enough to deal with multiple strategic LOC closures in both friendly and contested territories. It is safe to assume that in any scenario with degraded LOCs the concepts of decentralization and the use of openers will be critical capabilities.
QUADRANT 3
In the Quadrant 3 scenario, the information environment is degraded or blocked but the strategic LOCs remain viable. Again, the JLEnt may have to move away from an information-centric approach as the tools of the information age become degraded. The shift to capacity-centric strategy becomes easier with open LOCs, but it is still a challenge. A successful transition to the capacity approach will require logisticians to recognize early that the information-centric approach will not be adequate to sustain the force. Like the first scenario, this is not a possibility that current doctrine thoroughly explores.
In this scenario, the capacity-centric logistics campaigns of World War II in the Pacific may offer clues to successfully utilizing the LOCs in an information-contested battlespace. Preplanned push packages could offer a significant support capability in place of the current pull model. Push logistics falls squarely within a capacity-centric approach and can provide support despite a degraded information space. Should the campaign's nature change into something resembling the Pacific theater of World War II, the JLEnt will have to shift to a capacity-centric approach.
QUADRANT 4
In the Quadrant 4 scenario, an adversary can seriously harm the information network and hinder the ability to carry out logistics. This is the worst case for the joint force and the JLEnt. The multidimensional disruption could be carried out by creative and irregular methods that already exist. Web-based networks, critical to information-centric logisticians, could be brought down by cyberattack. Or worse, the adversary could infiltrate the web-based systems with bad data, causing logisticians to lose trust in the entire system.
Centralization of logistics information systems will be exploited to full effect. Strategic LOCs could be challenged in a variety of unpredictable ways. All of this is possible using today's technology. The future is likely to create even more disruptive capabilities for an adversary to use.
In this type of environment, an information-centric JLEnt will be severely degraded unless it can creatively adapt. This scenario could place enough demand on informational and physical systems that it will be impossible for the JLEnt to recover quickly. Because of the potential for a two-pronged attack on physical and information spaces, this scenario deserves more attention from logistics strategists.
This scenario could also bring about the paradox of disruptive technology. As information systems become more central to the JLEnt, their disruption could bring about a need for solutions that look much like a system that a pre-internet logistician would recognize.
The paradox is that the more technologically advanced the JLEnt becomes, the farther back it would have to go in technology to cope with the challenges of a contested environment. If information processes become irreversibly impaired, the capacity-centric approach may prove the only viable method to sustain the force. For example, pre-positioned supplies, a hallmark of capacity-centric logistics, will be critical if the LOCs are not viable.
Much of the doctrinal and future operating concepts assume that information will be contested, but information still persists as a central theme of future logistics systems. If the transition to a primarily capacity-centric system becomes necessary, it will represent a significant paradigm shift for logisticians and the JLEnt.
Another layer of complexity will involve information flow among the local area, the theater, and the national level of logistics. Cyberattacks could disrupt centralized logistics systems, but how will the operational and tactical levels be affected?
It is quite possible that the strategic information space could be contested but information could still flow up to that level by unexpected means. This scenario could also see a globally contested space but a relatively uncontested local area or theater information space.
A degraded information environment coupled with physical constraints on the JLEnt is the riskiest and most demanding possibility in the contested environment. Paradoxically, the JLEnt of the future may come to rely on aspects of the pre-internet logistics system while supporting the most technologically advanced military of all time.
The overwhelming success of the JLEnt in meeting combatant commanders' needs has led to a strong attraction to information-centric systems. Capacity problems have been rare, and combatant commanders have been free to focus on campaigns without significant logistics limits. To be successful in the future, logisticians will need to exercise influence in the JLEnt and will require the ability to communicate logistics limits. Capacity and information disruptions in the contested environment could set the boundaries of campaign plans.
As fog and friction degrade the JLEnt, logisticians must anticipate significant imbalance and volatility between information-centric and capacity-centric logistics. The volatility expected in the contested environment will challenge the JLEnt in new ways. The role of capacity-centric logistics in sustainment operations during war should not be underestimated. To prepare for the unexpected disruptions created by fog and friction, logisticians will have to prepare the JLEnt for the possibility of a return to capacity-centric concepts.
--------------------
Capt. Philip Lere is an Air Force logistics readiness officer and part of the Afghanistan-Pakistan Hands program. He holds a master's degree in strategic security studies from the College of International Security Affairs in Washington, D.C.
The author thanks George Topic and Christopher Paparone, Ph.D., for reviewing and contributing to this article.
--------------------
This article was published in the May-June 2017 issue of Army Sustainment magazine.
Related Links:
Army Sustainment Magazine Archives

Social Sharing