Six ethical hackers who protect U.S. Army Research Laboratory (ARL) computer networks rose to the second place spot in the Global CyberLympics World Finals.
The series of cyber challenges is touted as the world's first international team hacking championship.
ARL's Computational and Information Sciences Directorate support contractors from ICF International, who represented the U.S. in the World Finals held March 21 in Chantilly, Va. were not far behind the number one team during the span of competition. The Netherlands team won first place.
The CyberLympics offensive and defensive security challenges, sponsored by the E-C Council, mimicked real-world threats faced by professional hackers in the competition from Europe, Asia and the Middle East, Africa, South America and Australia.
Just months before the second-place title, Team ICF International members were unsure if they would be participants in the Maryland Cyber Challenge that swept them away 24 hours later to CyberLympics World Hacker Halted USA in Miami and ultimately gave them the ticket to compete internationally as the top U.S. competitor. Both first and second place competitors from the national-level matches were invited.
Participation will not be a question next year. The team would like to return for a win, said Justin Wray, a senior programmer with Team ICF International.
"The competition was intense and the teams were truly the best in the world," said Jay Bavisi, chairman of the Global CyberLympics Organizing Committee and president of EC-Council. "The fact that the lead changed every few minutes shows how much it takes to capture the hill and stay on it."
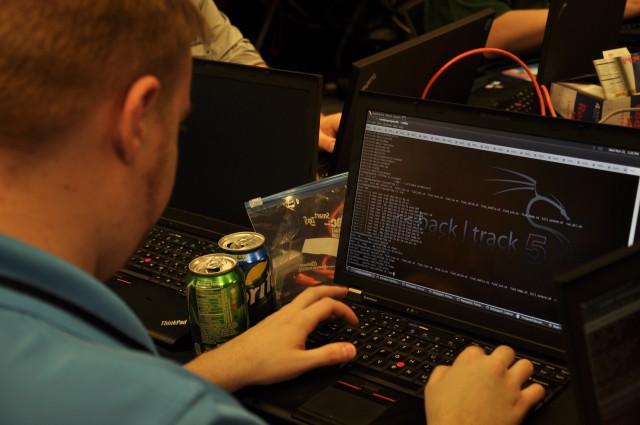
Forensics was the first round of the World Finals. Computer programmers had to find evidence of intrusions, discover malware, and track cyber attacks across multiple systems, then report their findings.
"For instance when a computer system is compromised at ARL, there is a thorough investigation to determine data regarding the attack and to prevent further attack and that data is communicated in a forensics report. We were very familiar with the processes that it took to do well in the first round," said Wray. "It was almost too easy. We thought there was a catch."
In the next round, the Pen Test, the goal was to assess a network of computers for vulnerabilities, discover valuable data that was not properly protected, and successfully exploit the vulnerabilities to gain user-level or administrative control of the computers. This round not only tested cyber defensive skills, but also teams' ability to report findings.
The last of the elimination rounds was Computer Network Defense, which challenged teams to protect networks from a live cyber attack. They had to detect and mitigate hacker activity and other misuses.
"ARL is extremely proud that our cyber defense team includes some of the top cyber experts in the world," said Dr. Alexander Kott, division chief, Network Science Division. "They had to employ cyber defense skills of exceptional breadth, depth and agility."
The competition is in some ways similar to the Cyber Defense Exercise (CDX) put on annually by the Department of Defense, Wray said. He participated in that and seven times in the Collegiate Cyber Defense Competition, another similar competition. He has been programming computers since he was 8-years-old.
"Competition networks are as similar to a real networking environment as possible," Wray said. "That is what makes these exercises valuable."
The CyberLympics culminated with a capture-the-flag challenge that allowed teams to use whatever network assessment tools were available to them to be the first to gain and retain control of the most available neutral targets (network systems), while not compromising their own network systems.
Wray and another team member, Ben Heise, developer/computer programmer, ICF International, met every day after work leading up to the international competition. "We would stay up half of the night working through potential scenarios," Heise said.
"It is a passion. Some people go to work from 9 to 5 and forget everything they were working on before they get out of the parking lot. We left work to go home and do it all again," Wray said.
"We monitor all sorts of agencies within DoD," said Bill Christman, ICF International, who manages the ARL account from Adelphi. "Our team has to be at a different level. We have to know both the technical and policy aspects of DoD network systems. We have to find and understand abnormal patterns. We have to create our own tools unique to DoD problems to detect and protect."
ARL is one of only 23 Computer Network Defense Service Providers within the DoD that is responsible for delivering protection, detection, response and sustainment services to DoD users.
Typically, people who work on the ARL support team, based at Adelphi Laboratory Center and Aberdeen Proving Ground, love computers, Heise said.
"There have been computers around my house as long as I can remember," Heise said. "My grandfather started out with a really old IBM with an 8086 processor. My family would lock me out of it for one reason or another growing up and I had to figure a way to get back into the system. I got quite good at it."
The capture the flag-type final round of the World Finals allowed creative, out-of-the-box thinking. They couldn't use tools from their organization, only open source or tools they created on the fly, said Wray.
"It was tight throughout, but towards the end of the competition I could see the focus and intent on their faces," Christman said.
"You don't compete without the goal of winning. At the moment you don't win, you feel like a failure, but we kept it in perspective, we are the U.S. champs and among the top in the world," Wray said.
Team ICF International includes Ben Heise, Jesse Hudlow, Mark Reinsfelder, Steve Collmann, Matthew Wines and Justin Wray.









Social Sharing