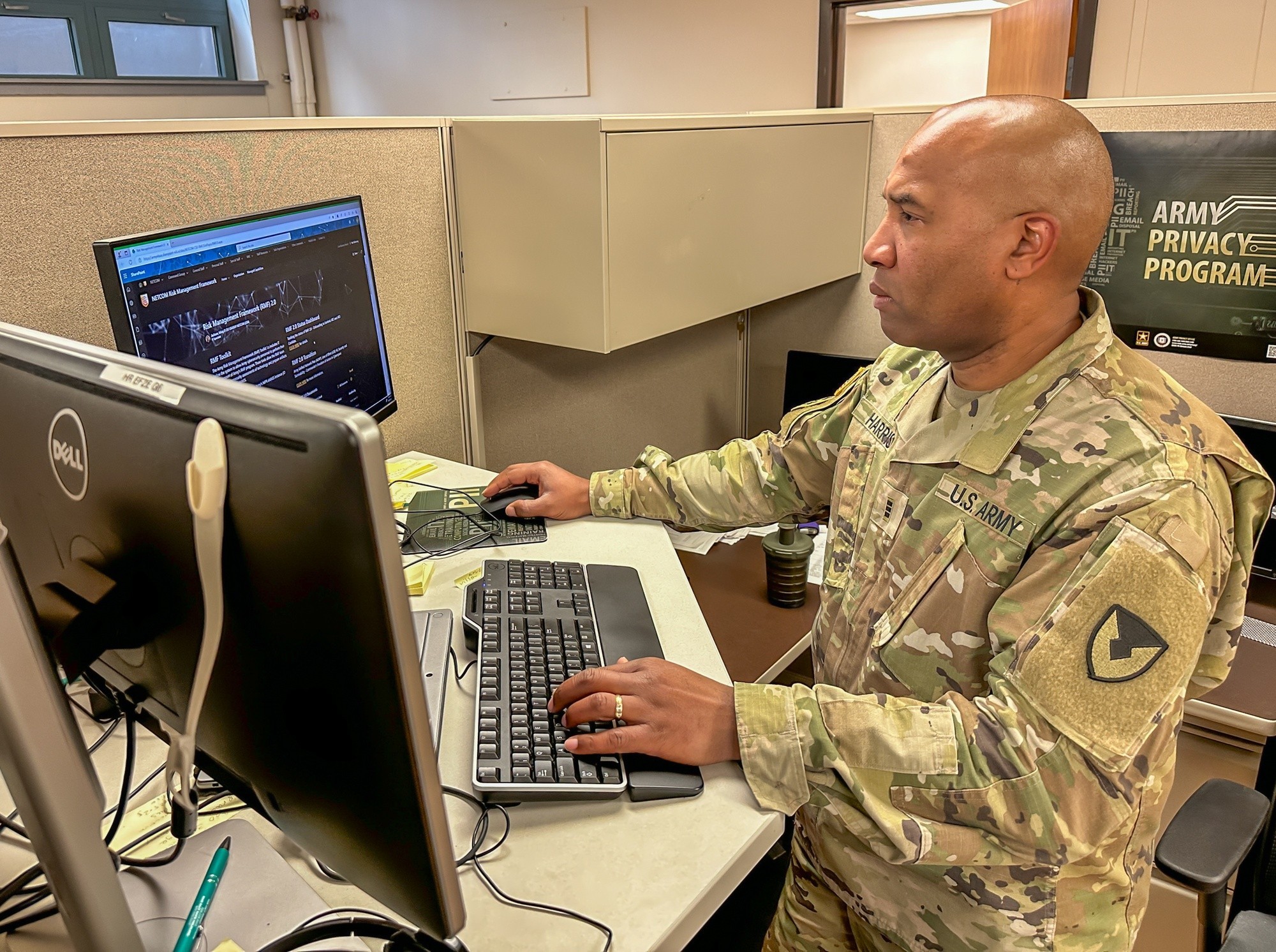
ROCK ISLAND ARSENAL, Ill. – Chief Warrant Officer 3 Dennis Harris has a clear mission: ensure that the essential information technology systems used by U.S. Army Sustainment Command are readily available to the Soldiers, Civilians, and contractors on the ground who rely on them.
Harris’ Military Occupational Specialty, or position, is as a 255A Data Operations Warrant Officer in ASC’s G6 (Information Technology) directorate. According to U.S. Army Recruiting Command, 255A Data Operations Warrant Officers are the “subject matter experts responsible for designing, building, configuring, operating, maintaining, and sustaining data and services in the Army’s portion of the Department of Defense Information Network within the cyberspace domain.”
At ASC, Harris is responsible for making sure systems critical to complete ASC’s mission, such as computers, software, or mobile devices, are available to the personnel on the ground who need to operate them. These systems are referred to as essential information technology systems by the ASC G6 team.
ASC’s mission is to provide globally-responsive strategic logistics capabilities and materiel readiness to enable combatant commanders to conduct the full range of military operations. In a nutshell, this means that ASC makes sure Soldiers have what they need, when and where they need it. To do so, though, personnel need Soldiers like CW3 Harris to ensure their access to essential information technology systems.
“Without essential information technology systems used by ASC, analyzing oil from significant pieces of equipment, verifying potential employees, identifying potential problem areas, managing vehicle inventory, or monitoring contractors’ performance would be nearly impossible,” Harris explained.
In order to allow personnel to have network connectivity on their systems, Harris follows a rigorous process, known as the Army’s Risk Management Framework, to get the systems to an acceptable level of residual risk.
“This process is intended to ensure DoD systems with digital capabilities, including National Security Systems, are engineered for cyber survivability,” according to Department of Defense Instruction 8510.01. “This is done by integrating controls that support security, privacy, operational resilience, supply chain risk management, and the best cyber intelligence, or commercial cyber threat information available at the system and organizational levels.”
Although Harris goes to great length to ensure the safety of ASC’s network, a certain level of residual risk must always be accepted, he explained. “Without the acceptance of risk by the network owners, ASC logistic Information Technology systems are prohibited from ever connecting to the network.”
Department of the Army Pamphlet 385–30 describes residual risk as “the risk associated with a hazard that remains after implementing all planned countermeasures or controls to eliminate or control the hazard.”
The Army’s RMF acts as a shield, safeguarding vital military systems from cyber threats and vulnerabilities. Harris's diligent application of the RMF ensures that ASC's information technology systems remain secure and compliant, supporting their mission-critical functions.
Working at ASC has given Harris the opportunity to think and plan at a strategic level, something he has not done previously in his career. “I am used to planning 12 months out for every mission/task. I am learning to think strategically, teaching me to project further (3-5 years) on a much larger scale,” he said.
He believes that his experiences at ASC will make him more of an asset at his next duty station. “It will add diversity to my resume and show the Army that I can adequately adjust when faced with tasks I have not encountered,” he said. “Not only will I be able to plan on an operational level, but I will also be able to provide strategic input to the next organization I am assigned to, making me a more diverse asset.”
Harris is proud of the work he has done at ASC because it allows other professionals to do their jobs. “In a time when everything is done digitally, soldiers would not be able to communicate using email, Teams, SharePoint, or telephone. It would be impossible to get anything done,” he explained.
“I chose this line of work because of the endless challenges,” Harris added. “There is a new threat every second, forcing IT (information technology) professionals to remain on alert as the first, second, third, and fourth line of defense when protecting our network from those who wish to harm our information.”
Does a career as a 255A Data Operations Warrant Officer interest you? Visit https://recruiting.army.mil/ISO/AWOR/255A/ to learn more and see if you qualify.
Social Sharing