In 1965, Intel co-founder Gordon Moore discovered a trend in the computer manufacturing industry. He noticed that every two years, the number of transistors on a microchip doubled. From this observation, he predicted that the computers of the future would become exponentially faster and more powerful while also becoming smaller and more affordable.
Later known as Moore’s Law, his prediction is responsible for explaining the accelerated rate of today’s technological advancements. It’s thanks to Moore’s law that everyday conveniences, like cellphones, have progressed from the blocky Motorola DynaTAC 8000X, which cost nearly $4,000 retail and offered only 30 minutes of talk time, to smartphones that cost only a few hundred dollars and are capable of providing handheld control for almost every aspect of our lives.
Because of Moore’s Law, we’ve developed more new technologies in the past 50 years than we have during any other stretch in human history. With this constant turnover in technology generations, our lives are more streamlined, efficient, and convenient. However, as our day-to-day activities become more intertwined and connected to one another, they also become more susceptible to risk from malicious actors, such as hackers, and our businesses, municipalities, and infrastructure are having a difficult time keeping up with the constant change.
To help address this growing threat, the Connecticut National Guard, in a partnership with the University of New Haven’s National Security Agency Center of Academic Excellence in Cyber Operations, participated in Ironclad 2021 June 21-25, a weeklong course designed to provide knowledge and understanding of how to respond to cyberattacks.
According to the Center for Strategic & International Studies, at the time this article was written, there have been 56 significant cyberattacks around the world this year. Cyber threats against the United States are nothing new, but following allegations of foreign tampering in our elections and known malicious activity such as the ransomware attacks against the Colonial Pipeline, the JBS meat processing company, or more locally, against Hartford Public Schools in September 2020, the need for greater cyber protection has become evident.
In response to this growing 21st century threat, President Joe Biden signed an executive order to improve the nation’s cybersecurity capabilities on May 12, 2021, but the Connecticut National Guard and Department of Defense have already taken steps to increase the amount of quality and applicable training for its cyber warriors.
The first iteration of Ironclad 2021 came directly on the heels of the annual Cyber Yankee exercise, which brought together Soldiers, Airmen, and Marines from across New England to respond to simulated cyberattacks against public utilities around the country.
Unlike Cyber Yankee, Ironclad 2021 was designed not only for Guardsmen who already possess a cyber-related Military Occupational Skill or Air Force Specialty Code, but any traditional Guardsman who may have a civilian career in the cyber industry or an interest in cybersecurity.
“Everyone that’s in the class comes from a different background,” said Chief Warrant Officer 3 Michael Smith, an Information Services Technician with the Connecticut National Guard’s Defense Cyber Operations Element. “We have a lot guys from the Air Guard, we have guys from the Army Guard, and we have guys who aren’t cyber professionals in their [National Guard] job. One guy here is a [Cable Systems Installer-Maintainer], he runs cable for the signal company, but gets to come to something like this and it exposes him to a completely different set of skills, to something he doesn’t get on his one weekend a month, two weeks a year.”
U.S. Army Maj. Ryan Miller, the Connecticut National Guard’s State Cyber Operations Officer, said opening this course to a wider selection of Guardsmen gives him access to a broader pool of trained personnel capable of assisting in the event of another local cyberattack, like the Hartford schools ransomware attack, but also serves a larger goal to increase these Guardsmen employers’ first line of defense against cyberattacks.
“This class is nice because it’s an opportunity that we never get within the Guard,” said Smith, who works as a cybersecurity manager for Pratt & Whitney. “The expertise of the instructors with reverse engineering software is something we never see in our normal training regimen, so this enables us, if we’re called on for an instant response, to look at things a little differently. Even if we’re not going be the ones who will be deconstructing any kind of malware, we can assist with tailoring a response to different places because you’re never going to have a one-size-fits-all response.”
The class also focused on Industrial Control Systems, or ICS, and their vulnerabilities for attack. These ICS used to be individual, offline systems that were used to control a single entity such as a pipeline or manufacturing node.
With the rise of the internet and cloud-based software, companies are now able to interconnect these different systems to collect information and gather them in a centralized database in order to make quicker and more unified business decisions.
When these systems were offline, they were immune from remote entry, making stealing or manipulating data impossible without plugging directly into the onsite computers. Once these systems were moved online, however, additional security measures needed to be made in order to prevent this unwanted access and need to be constantly monitored and updated to remain vigilant against hackers’ evolving tactics.
“Where I work at [General Dynamics Ordnance and Tactical Systems], we’re part of the defense industrial base … we manufacture a lot of the munitions systems and armament that the U.S. military uses and these ICS systems are what we use to manufacture it,” said Tech Sgt. Matthew Meyers, a Cyber-Warfare Operations Specialist with the state Defense Cyber Operations Element. “So having an in-depth knowledge of how they work, how they might be attacked, and the risks that are involved when you start plugging them into your corporate network and letting them have access to the internet is really important.”
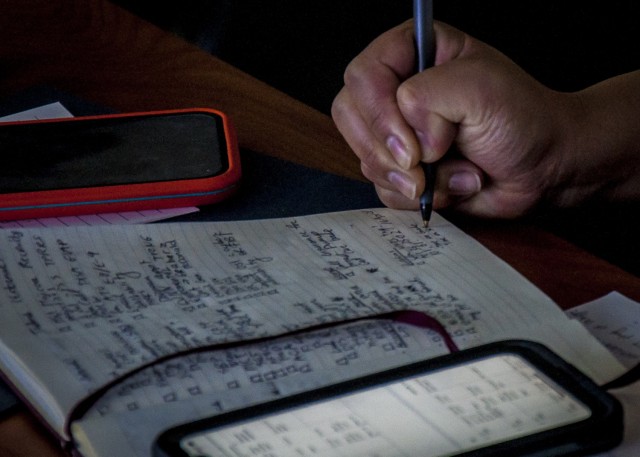
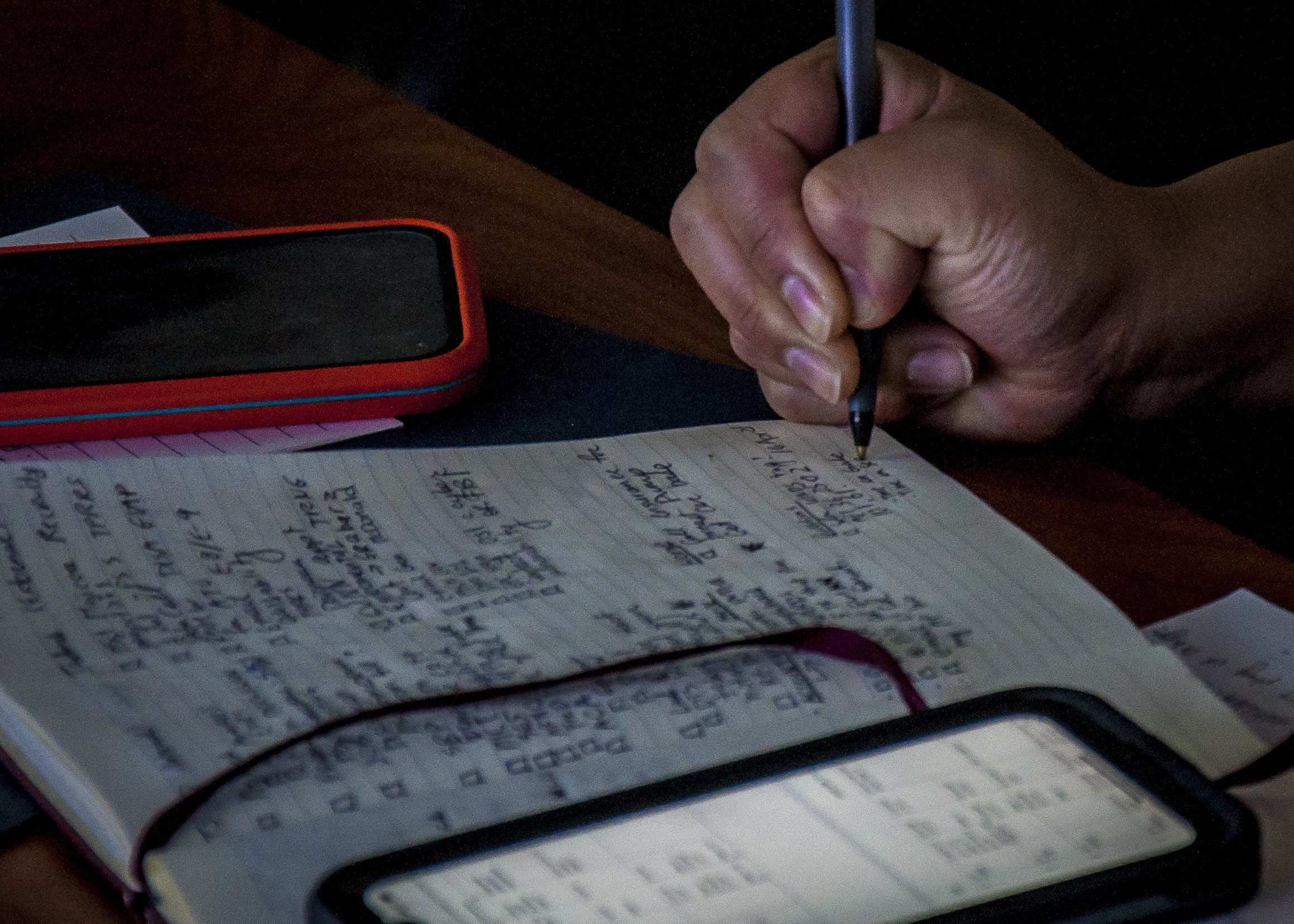
Ironclad 2021 was paid for with a grant issued by the National Security Agency and taught by civilian contractors who possess years of experience handling the cybersecurity for organizations similar to those the National Guard may be called upon to assist in the event of an attack. Students were housed on campus and spent the day both in lecture and with hands on practical exercise. In the evening, students participated in digital scavenger hunts and games of capture the flag to reinforce the lessons of the day.
As soon as Ironclad was announced, demand for attendance quickly outgrew the available seats, forcing Miller and his staff to create a waiting list. With such an overwhelming response, Miller is hoping he can tack Ironclad 2022 onto the first week of next year’s Cyber Yankee exercise, which the Connecticut National Guard is hosting. By opening the class up to more Guardsmen from neighboring states, he hopes to expand upon already existing relationships with his partners throughout New England and create a more robust cyber defense force for the National Guard.




Social Sharing