The Army and joint forces conducted Cyber Forge, a Persistent Cyber Training Environment, or PCTE, event in June at the Johns Hopkins University Applied Physics Laboratory, or JHU-APL, in Laurel, Md.
Participating cyber warriors were given a mission to execute an incident response, hunt and cyber posture of a potential compromise of fictional DoD industrial partners.
Designed, planned and overseen directly by the Navy using the PCTE prototype platform, Cyber Forge brought together, the exercise brought together U.S. military program leaders, program managers, cyber protection forces and industry to further the capabilities for persistent cyber training.
"Cyber Forge is a live-fire cyber training event," said Army Lt. Col. Thomas R. Monaghan Jr., product manager for Cyber Resiliency & Training, Program Executive Office, Simulation, Training, or PEO STRI, Orlando, Fla. "There are cyber mission forces here -- three onsite and three distributive -- one in Hawaii, one in San Antonio, Texas; the other is at Fort Gordon (Georgia)."
Navy Cyber Protection Teams, or CPTs, 02, 90 and 94, from Fort Meade, Md., were onsite. Remotely participating were the Air Force's 67th Operations Support Squadron, at Joint Base, San Antonio, Texas; the Army's 155th Cyber Protection Team at Fort Gordon, and the Navy's Cyber Protection Team 26 in Kunia, Hawaii.
"The PCTE is the platform they are using to conduct this training event," said Monaghan. "Cyber Forge is literally the next training event where the cyber mission forces set up a couple sets of task missions and standards to accomplish the specific training goals. This time they're actually doing some assessments of some of the teams, trying to push the PCTE system further, farther and faster."
In the exercise's fourth day, Monaghan said, "From a platform perspective, the system is performing well -- no major issues. We've injected a couple of additional capabilities for the cyber mission forces to use."
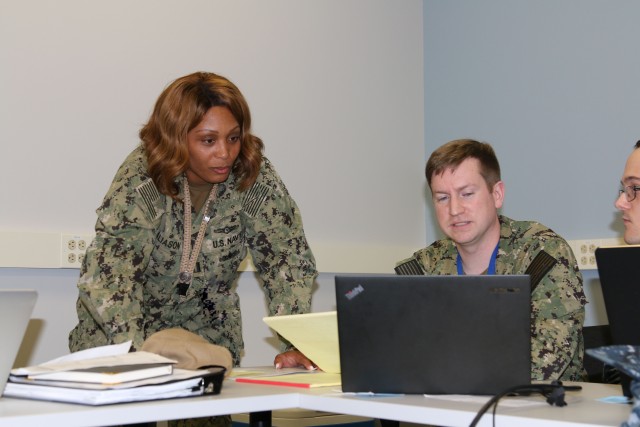
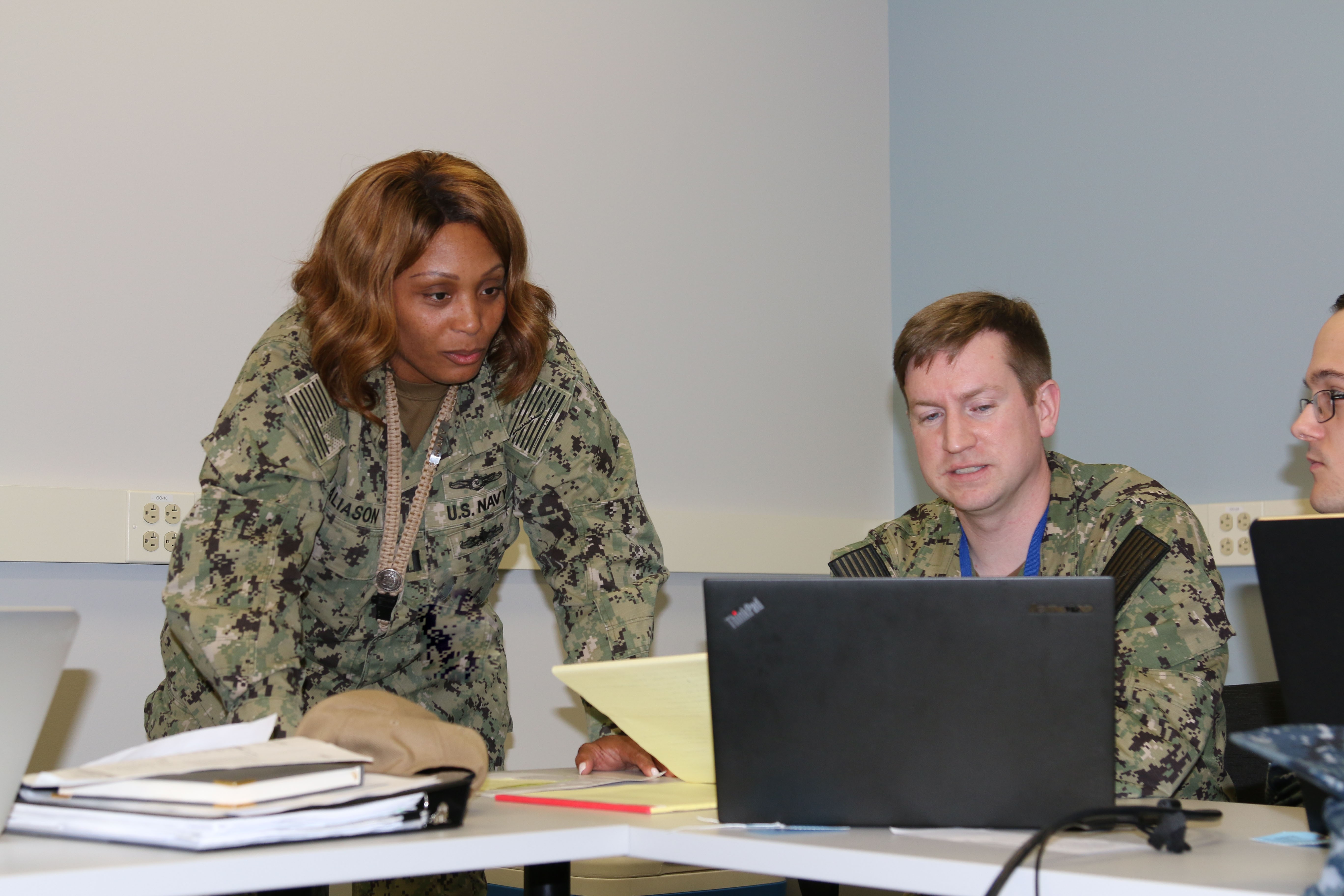
Navy Lt. Michelle A. Aliason, team lead for 02 CPT, with more than 20 years Navy experience in network operations, information systems and information assurance, served as a liaison for her team.
Aliason said her role in the exercise was to serve as a conduit between her team and higher headquarters to ensure that the desired end state of leaders and commanders at all levels of the event were being met.
"Anything that happens at this level that generates a commander's requirement for information, I push up to the appropriate authority," she explained.
"For Cyber Forge, essentially we're here to exercise our ability to hunt effectively on the network, (and) engage with the customer, -- ensure we're providing them with any information they need to properly defend their network.
"We're looking for cyber actors, malicious activities, anything we see that's not normal to the customer, identify what those are and make mitigation recommendations."
She said that by day four her team found what they thought was suspicious activity and validated that with the mission owner. We have some suspicious employees, not confirmed yet -- we're working with the customer to identify if this is normal activity," said Aliason.
Navy Petty Officer 3rd Class Richard Bradley, a network analyst also from CPT 02, said that his team has come to APL several times.
"This is the first time I've been part of a training mission," said Bradley, a two-year Navy sailor. "This training showed me deficiencies that I had.
"We used a program called Splunk to look at different network traffic. I thought I was a lot better than I am. It helped identify things I can work on.
"It also gave me confidence in the things I knew how to do. It gave me a feel on how we would do our mission. I haven't been on the team very long. It's been great for learning how everything's going to go."
Army Chief Warrant Officer 4 Kris Everson of the Cyber Protection Brigade's 1st Battalion, was onsite to evaluate the progress the PCTE has made in delivering gunnery tables to his team.
"One of our teams is participating in the exercise," said Everson. "I did some coordination with getting them to the environment on the range and working with the Navy."
The PCTE is an environment that brings together different commercial defense companies, that provide an environment to train to provide an environment for 24/7 training to team and individual work specifications, to team and individual work specifications that provides the user the ability to train 24/7, said Everson.
"The teams are given a scenario to evaluate the network, to find the actors that are attacking the network, find anomalies within the network and then provide remediation to the local unit," said Everson, formerly a 16-year enlisted signal Soldier and now a warrant officer who has served three years in a cyber Military Occupational Specialty.
"PCTE provides an easier avenue for the forces to train together without having to be located in the same area," said Everson. "It provides an environment where everybody can collaborate, train on the same range or different ranges."
Joining Everson was Army 1st Lt. James Gusman, operations (S-3) SIMS officer-in-charge for Headquarters, CPB at Fort Gordon, one of the first two cyber officers directly commissioned into the in Army from the tech industry.
Gusman said his primary goal and mission are the integration of PCTE into the brigade's environment for teams and individuals to start using the training, moving forward as replacement for the existing system and infrastructure that they have.
"One of the things I think the PCTE brings to the table is multi-vendor," said Gusman. "The PCTE allows us to take a lot of what we see out in the field, develop it in an environment and practice against those real-world situations, or what we might foresee in the future being a real-world or live situation, either with units or going on in real production environments, whether that be certain military installations or environments, things like that."
Jeff Tucker with Cyber Defense Activity 64 at Fort Meade offered this perspective.
"We wanted to find a way to train our team from start to finish on a simulated mission, from a team first receiving orders and working with the customer to the debrief that is delivered to higher headquarters at the end," said Tucker. "Up to this point there has never been a way for us to be able to do that."
Working with PCTE, some of the Sailors developed a scenario that included intelligence they might see on a real mission, built the simulated range, and developed a way to evaluate a team.
"They did a fantastic job and created the outcome that we were looking for," said Tucker.
"Each team had to come in and give the initial customer brief, describe who they were and why they were there, and what benefits they brought to the company that might have suspected actors within their network.
"Each team was evaluated by an external 'white cell' team member, but the scenario also provided a way for each team lead to internally assess and evaluate their own personnel while working on a target. It showed each team members strengths, how they communicate, and how they organize a hunt operation in a way they haven't been able to before.
"For the first time, we are practicing how we should fight in a training environment that is goal-oriented and not task-oriented. That is a big deal. We want each team to be able to accomplish the goals they are there to meet.
"We have young personnel coming in the military all the time and with technology constantly changing, their way may be better. We just care that they find what they are looking for and take the appropriate action."
The event also brought several PCTE contractors together with the forces.
Lee Rossey, chief technology officer for SimSpace Corp., said vendor support ensures that the platform and the event go well.
"There are a number of vendors here as part of the PCTE platform," said Rossey. We're just here to make sure the platform is doing well and get feedback.
"PCTE's going through this prototype phase and we're going through a series of events like Cyber Forge. After each event we want to get feedback from the operators that it's doing what it intended to do, making sure that feature requests are getting adjusted.
"So the program is going through a series of major updates. The 1.0 version is due to be released in January 2020. These are incremental updates that are being made, maturing the platform."
"Cyber Forge is an event being run to demonstrate the forces' ability to develop and execute their own training within the PCTE platform," said Sean Donnelly -- founder and chief executive officer of Resolvn, Inc. "As it relates to us, we are here in conjunction with Cyber Forge to demo 'what's ahead'."
While all these units are here seeing different teams training how they're going to fight, they're also getting a view of the next level of PCTE.
"As operations tempo increases, teams can't afford to spend man-hours developing all the content.
PCTE needs people to build the in-range networks, the training, and the challenges. That's what we do," said Donnelly. "We've built range-based content packages that challenge teams in operationally relevant scenarios."








Social Sharing