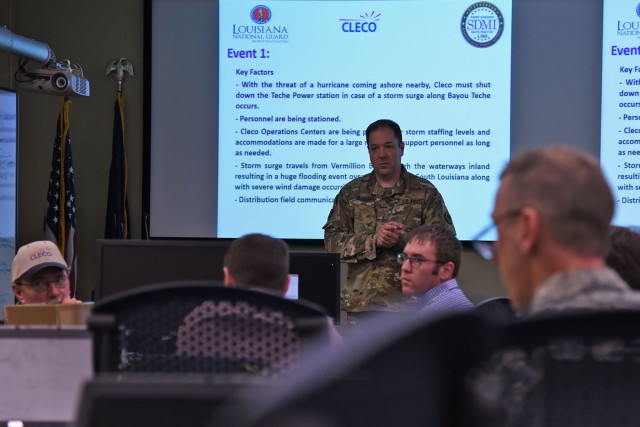
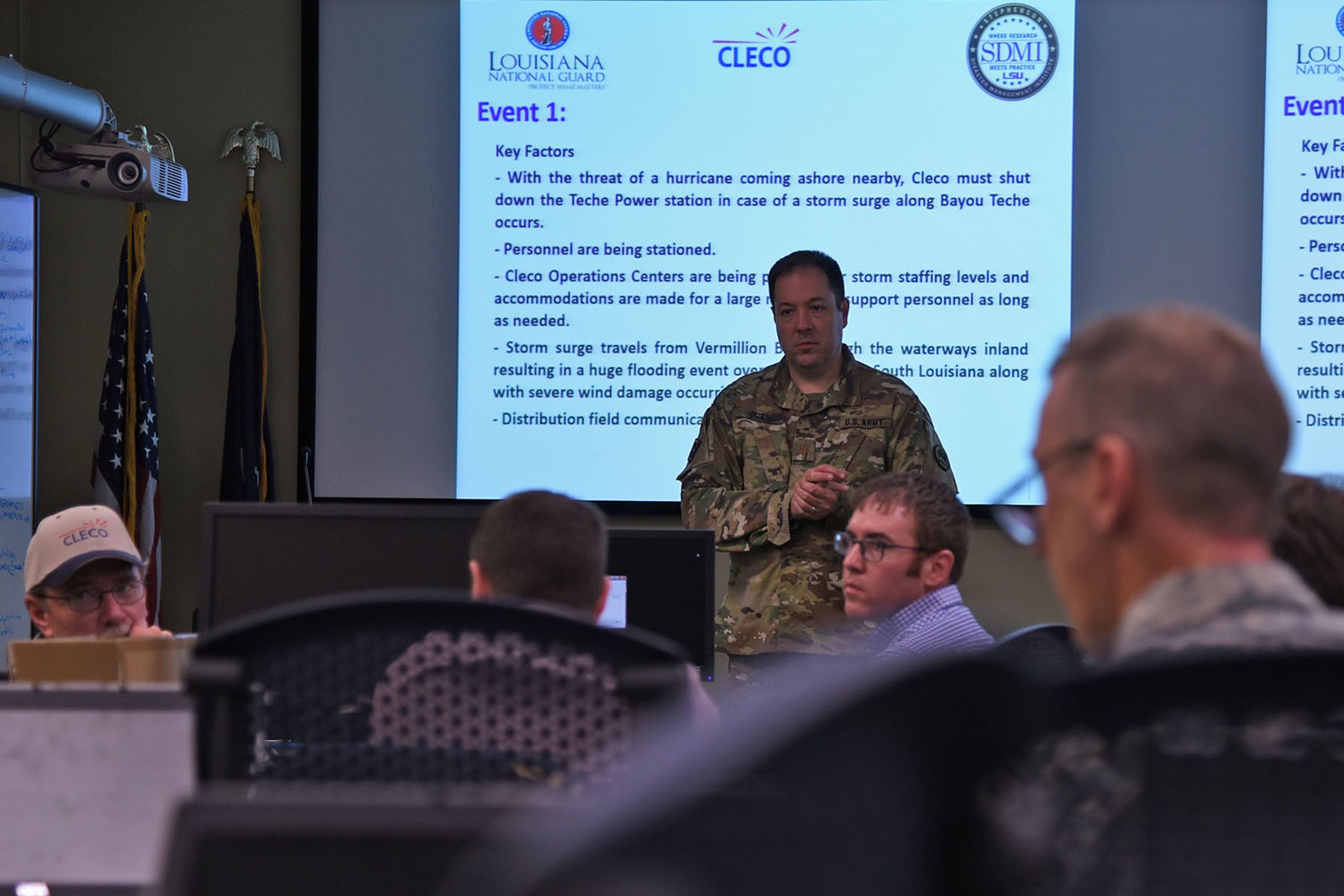
NEW ORLEANS -- The Louisiana National Guard's cyber protection teams, the Federal Bureau of Investigation and the Department of Homeland Security, held a four-day training seminar with Louisiana power supplier CLECO, as a part of the LANG's annual disaster relief exercise, March 29 -- April 1.
Held at the Louisiana State University's Stephenson Disaster Management Institute in Baton Rouge, the LANG's Cyber Defense Incident Response Team (CDIRT) and Defensive Cyber Operations Element (DCOE) trained CLECO employees on how to recognize and respond to cyber threats, as well as when to ask for help if a threat is detected.
"What we are trying to do is identify the malware," said Mark Northrup, chief information officer of CLECO. "Malware is the common word used for viruses, worms or any other things called ransomware out there today.
"As with many other critical infrastructure companies," said Northrup, "we place a high priority on our cyber security resiliency and we are working with the National Guard to help us train and be prepared for any kind of incident so that we can ensure that our electrical delivery is never compromised."
The LANG has a cyber range where a cyber-attack can be emulated for training purposes.
"Like perfecting a golf swing at a driving range, this is how we practice our skills at the cyber range," said Maj. Allen Dunn, commander of the 10-man, full-time DCOE. "When we work with one of our critical infrastructure companies like CLECO, that makes Louisiana more resilient to cyber-attacks."
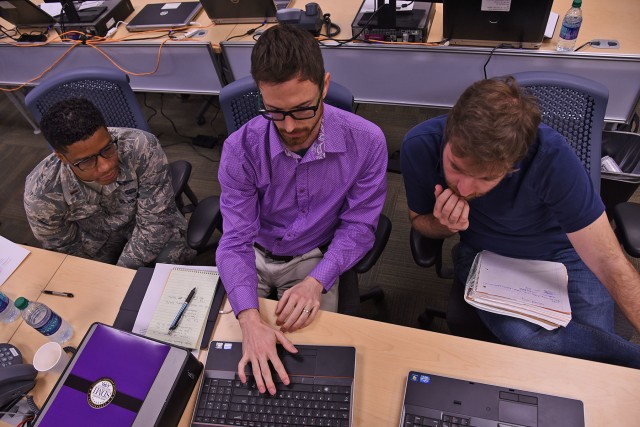
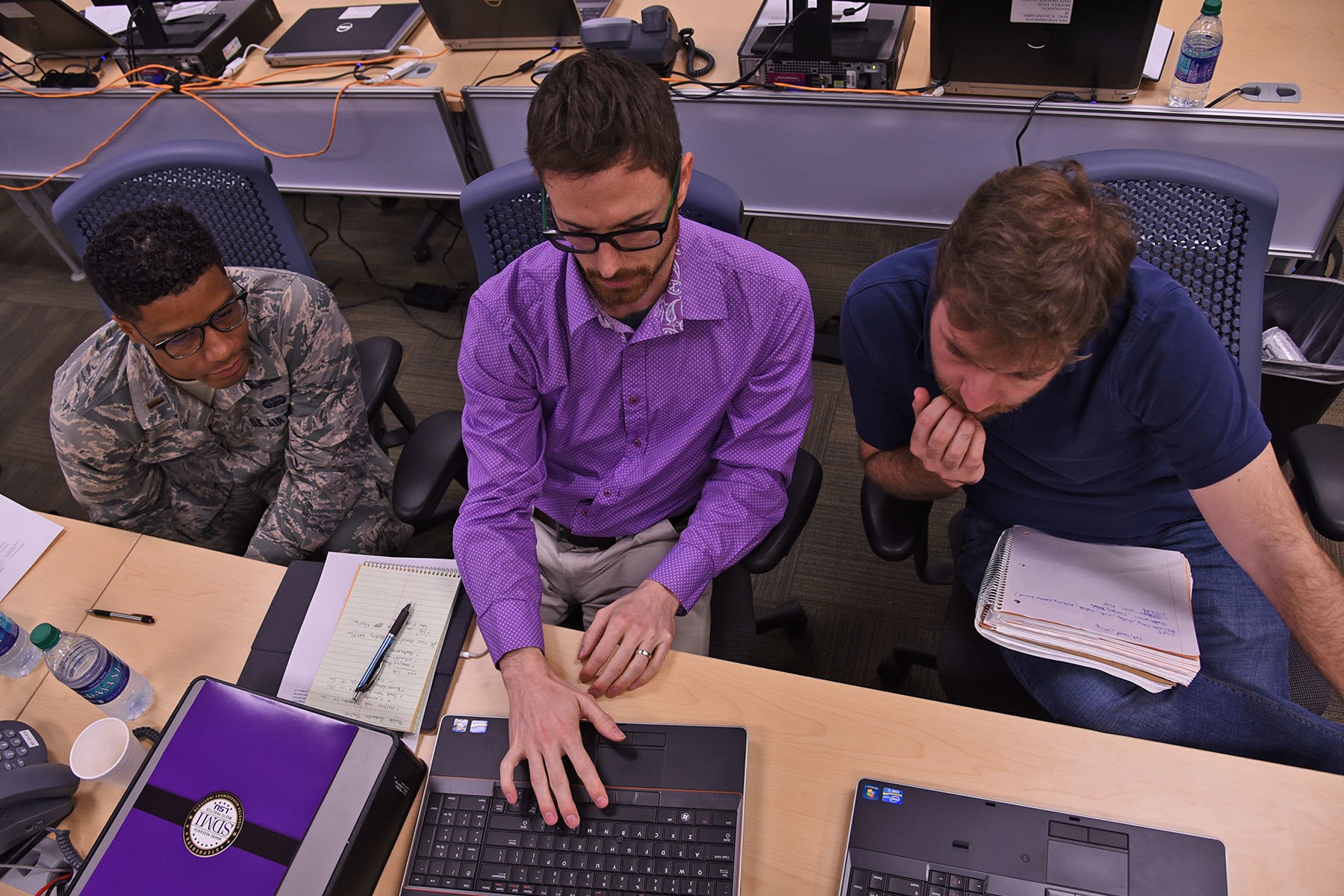
Dunn said that one of the main things the training is focusing on is forensics, or how to detect any incidents that may be happening in an environment and how to collect that data to turn over to authorities for prosecution.
"This training is beneficial to us so that we can understand the types of things that we may possibly deal with," said 2nd Lt. Eddie Dollis, Jr., a New Orleans native of the 214th Engineer Installation Squadron and a member of the CDIRT. "It's hard to walk into a network without any knowledge of that network or their processes and then try to respond to something."
Dunn and Northrup both stressed the importance of the LANG's cyber security teams training with local infrastructure companies. They also said that familiarity with the employees of those companies and standard operating procedures specific to each company makes the integration easier, if an attack does happen.
"It's very important that we do these exercises to create and maintain our partnerships with state agencies and to make sure that our skills are honed so we can respond properly in the event that there is a cyber-attack," said Dunn.
Cyber training for the LANG's teams will continue next month at the National Guard Bureaus's two-week long Cyber Shield exercise in Salt Lake City, Utah. Lt. Col. Henry Capello, LANG's information officer and cyber planner, said the exercise is vital for cyber defense and that he believes in training collectively before an event instead of scrambling to respond after.
"We embrace the concept 'train as you fight' and this is the only place where we can have a full scale exercise with all the key components -- from critical infrastructure companies who have a threat in their system, all the way to our Soldiers who are going to respond and provide military assistance to civilian authorities," said Capello.
He said the bringing together elements from multiple states and agencies prepares the LANG for such an attack.
The LANG's CDIRT is comprised mostly of Army and Air National Guardsmen that have a civilian job in a cyber-security field. The team was stood up in 2012 and conducts training quarterly. Since 2012, they have worked with several parishes, agencies and cities to increase interoperability and cyber-security operations.


Social Sharing