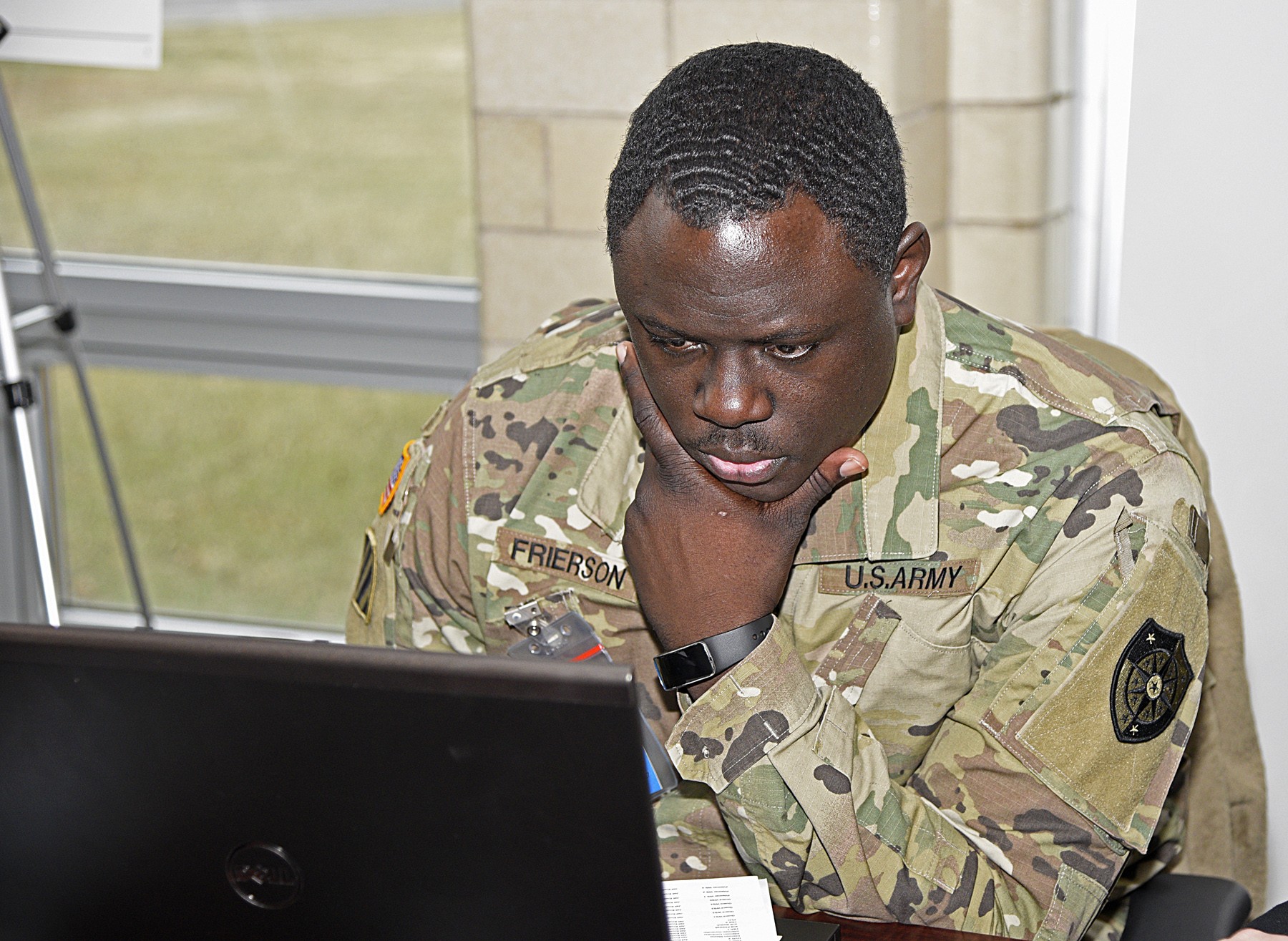
Soldiers from the Army's 154th Cyber Protection Team, or CPT, at Fort Gordon, Ga., took their defensive positions Jan. 10-11 for Cybertropolis STX, a live cyber exercise held at Muscatatuck Urban Training Center, Butlerville, Ind.
They conducted a cyber situational training exercise or STX, using an STX training platform to conduct a live, scenario-based STX as a new model for team-based sustainment training.
Their goals were "to deploy to the site with their equipment, connect their equipment to the mission network and conduct defensive cyberspace operations, or DCO, on the mission network," said Maj.Joe Marty, the 154th team leader.
In the exercise scenario, city hall and prison systems had been compromised by a network breach resulting in a request by civil authorities for Army support to neutralize and eliminate the attacks.
The 154th previously attended the Advanced Cyber Protection Team -- Pilot course after their first incident response mission, a six-week immersive training course held in Camp Dawson, W.V. where 12 members of the team were trained to conduct effective DCO.
Their mission as the Blue Team (defenders) was to detect and counter a variety of threats including: anti-virus evasion, network enumeration, ransomware, client-side attacks, pivoting,
network service exploitation, privilege escalation, attacks against industrial control systems and Windows' domain attacks.
Upon the exercise start, or STARTEX, the work priorities were to validate the network map, identify key terrain and critical assets (i.e., those services or systems that the business owner required to keep running throughout the mission), harden and monitor the key terrain & critical assets, and defend the key terrain and critical assets from the Red (aggressor) team.
"We establish trust to enable effective operations," said Marty. "Everyone on our team trusts that everyone else is doing what they are trained and tasked to do, or they ask for help."
A tenet of the exercise was to challenge the CPT's existing skills rather than merely lock out the Blue team or for the Red team to be locked out.
For this exercise, there is a coordinate cell consisting of the team lead and an intelligence analyst.
There also is a host hunt cell that focuses on host investigation.
A network security monitoring, or NSM, cell works on analyzing network traffic for indicators of compromise. They are like scouts on the network.
The harden cell is a separate team only during exercises because there is rarely cyber security provider personnel provided to implement hardening measures.
In real-world missions, the supported organization normally executes all hardening, and the CPT provides recommendations and guidance when needed. Normally the hardening personnel are integrated with the host hunt and NSM cells.
For this exercise the team relied on these two hardening personnel to use Active Directory, Group Policy Objects and firewall rule updates to harden the business owner's network and assets during the mission.
The team follows this sequence on typical missions.
Normally they would spend the first entire day (or longer) just observing and learning the environment to determine the baseline.
The baseline the team is observing may include adversarial/malicious activity. They rely on feedback and interaction with the business owner to establish a more accurate baseline of what "normal" looks like on their network.
Once a baseline is established, the CPT monitors the network and hosts with focus on the key terrain -- those assets that provide a marked advantage to enabling Red and Blue activities.
During their encounter, the 154th CPT Soldiers observed the attackers act inside of a network in various ways, and conduct an interactive battle against attackers on the prison systems.
At the same time, the attackers would escalate and respond in real-time based on the CPT's actions.
The adversary accessed the Human Machine Interface, or HMI, and employee workstations.
Once the lead host analyst went to the jail for physical access to the HMI to obtain the user accounts and investigate them for indicators of compromises, the team terminated the connections the adversary had on the HMI upon reboot, and changed the passwords for all the user accounts.
This password update turned out to be the key to victory, as the Red Team failed to establish enduring persistence on the HMIs, hoping to rely upon the stolen credentials.
Also the team saw port-scanning from a particular IP address on "the Internet."
Later, immediately preceding a ransomware attack on one of the hosts in the HR enclave, the team saw an http GET request to that same IP address conducting the port-scanning earlier. They saw the use of PowerShell in the StartRun box to execute a drive-by download, and they suspected the initial entry was gained via phishing email that exploited the human who opened it.
The adversary's actions on the objective were credential harvesting, data exfiltration, and their end goal was to unlock the jail cells at 3 p.m., which they failed to do.
Marty described the exercise as a success citing that given seven hours to defend the jail cells from being opened, they spent the first six hours observing the adversary on the network to determine all of their activity and methods of persistence that could be defended against all at once.
"We came with a plan, and we updated from that original plan throughout the mission," said Maj. Marty. "Our team adapted and overcame setbacks. We had several NSM tools that failed to work, so our NSM analysts had to rely exclusively on Bro, an open source, UNIX based network monitoring framework, to hunt for adversary presence on the network. Our host analysts used GRR and Kansa -- two new tools in the team's kit that hadn't been used in previous missions or exercises. Without access to standard network mapping tools, they relied on nmap to validate the network. The team used native and open-source tools because they were operating on a commercial exercise range.
"We remained focused on our mission throughout the exercise. We didn't get rattled by the red herrings thrown at us (e.g., ransomware on user workstations, data exfiltration). Our mission was to defend the jail cells from being unlocked, so all of our efforts focused on that.
"We demonstrated tactical patience by documenting our findings throughout the day, building the big picture, and developing the plan of counterattack (i.e., comprehensive change request) to be delivered close to the adversary's time on target.
"Finally, our team has trust. We trust each other because we have a lot of experience working together. Everyone in the 154th CPT trusts that their teammates are just as committed and industrious as they are, nobody slacks. When someone has an issue, they raise the issue to call for help."
"Cybertropolis provided our team the most realistic training environment we have encountered." said Maj. Marty. "We hope other CPTs get to experience this"










Social Sharing