Army Cyber Institute
West Point, NY 10996
contact.cyber@usma.edu
NEWS RELEASE
FOR IMMEDIATE RELEASE
Cyber Talks seeks innovative disruption -- Sept. 12, 2016
New York -- Challenging assumptions, thinking differently about potential adversaries, and building trust between the public and private sectors are critical to the future of cybersecurity, a diverse group told the gathered audience at Cyber Talks NYC Sept. 8 at the Hamilton Customs House. The Army Cyber Institute at West Point hosted the one-day event, their fifth such assembly and first in New York City.
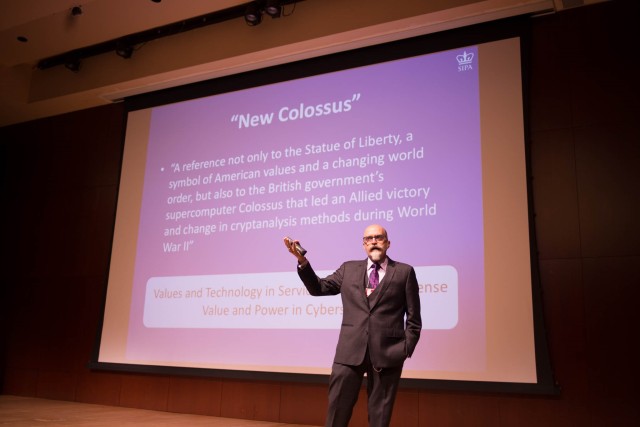
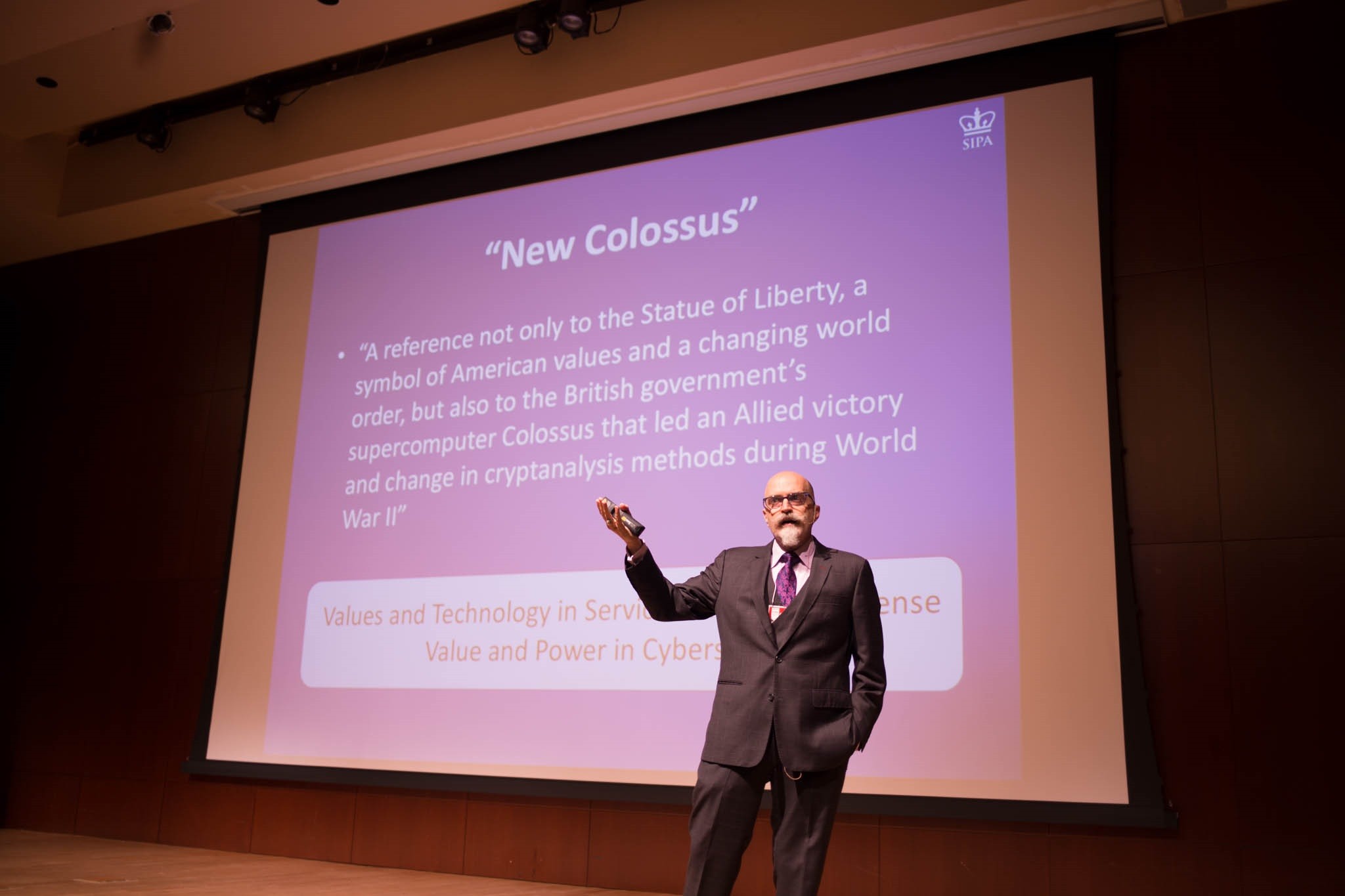
Presenting at Cyber Talks NYC were 11 thinkers and leaders. Each 20-minute talk focused on an experience or research effort and was designed to challenge the audience's assumptions. The topics loosely revolved around the theme of "New Colossus," a dual reference to the nearby Statue of Liberty, originally dedicated as the 'New Colossus,' and a British computer used during World War II to crack German codes. Both were seen as preceding a shifting world order, just as the internet and cybersecurity are changing today's world.
Col. Andrew O. Hall, director of the Army Cyber Institute, welcomed the audience and explained his rationale for choosing New York City. "New York City is a hub for so much of what we hold dear in the United States: it's an innovation center. The greatness of New York City is part of everything we are as Americans."
Bringing Cyber Talks to the city was a unique opportunity to bridge the military and the civilian technology communities, he added, noting that the audience included the tech and financial sectors, service members of all branches, academics and students, and civil servants. Also attending were cadets from West Point and regional university ROTC detachments, many of whom will perform cybersecurity roles in the armed forces.
Gen. Keith Alexander, the former NSA director and CEO of IronNet Cybersecurity, delivered the day's keynote address and encouraged the audience to challenge assumptions. "Most of the things we've been brought up to believe have to be challenged for us to defend the nation," he said. He warned the audience not to assume the U.S. would not be attacked on the national level in cyber because it had never happened. "Be ready. Challenge those assumptions. Prepare for what's coming our way: assume the worst and hope for the best."
Alexander said that events like Cyber Talks NYC were important to bring the military and tech communities together, enabling them to learn from one another, and ensuring they are ready to work together side-by-side, both ahead of and during a crisis. "How do we get people to work together when there is distrust," he asked the audience. Understanding and sharing facts is important, he said, and related his experience cooperating with an external review panel while director of the NSA. "What I learned from that: when people get the facts, this isn't hard. They don't have the facts. That's what we've got to help do."
The gap between government and industry is bridged by trust, he said. "Our military, our intelligence community, cannot defend this country in cyber unless we work with industry." If government and the private sector come together, we can collectively build a defensible cyber architecture for our nation and our allies. Incident response is not enough, he said. Government cannot defend industry if it does not know they are being attacked.
Jason Healey, a senior research scholar at Columbia University, delivered the opening keynote, discussing the transformational nature of cyberspace. "The internet is probably the most awesome technological artifact that has sprung from human minds and hands in the last 600 years," he said. He challenged the audience to question whether it works the way they think. Military discussions of cyber operations often loses sight of cyber's transformational nature, he said.
Even though the US military undoubtedly understands tactical and technical operations, we are probably missing something more fundamental in our understanding about how this works at the operational and strategic level, Healey said, citing the 2008 cyber-attack on Estonia. Often discussed as a tactical defeat, the years since have demonstrated a decisive victory for the Estonians. "If we can't tell the difference between a loss and a win, maybe cyber space isn't operating the way that we think," with critical implications for our understanding of military cyber power. We know cyberspace is different and should always be looking for clues if the dynamics actually work the way we think they do, he said.
Healey also cautioned the audience to carefully consider disruptions and escalations in cyberspace. "We need to be thinking about these medium-term and long-term national security outcomes," he said. Without thoughtful planning and policy, cyber space will devolve into chaos. He cited scenarios in which the internet might become like a failed state or a luxury good, unavailable to the masses. "In the best of futures, secure broadband connectivity, anywhere in the world is a global human right. That's the future that we want our kids and our grandkids to grow up with."
One of the best received talks came from a cybersecurity outsider, Andy Cohen, a former marketer turned lecturer and advisor. Cohen warned the audience that assumptions act as barriers and are often subconscious. He described assumptions that often lead organizations awry, such as assuming their people are smarter than their competition. "If there's any industry that's going to challenge that assumption it is in cybersecurity. Because as soon as you start feeling that you're the smartest, that's when you're really in trouble because there's going to be somebody who's smarter than you are," he said.
Fernando Maymi, the Army Cyber Institute's deputy director, and Chief Warrant Officer 3 Judy Esquibel described 'Jack Voltaic,' a cybersecurity exercise held in collaboration with Citigroup and 25 other corporate, academic, and government organizations. The exercise brought together representatives from critical infrastructure sectors including finance, energy, telecommunications, emergency management, and city government to respond to a two-day simulated cyber-attack against New York City.
The exercise included a "live fire" track, in which technicians used a specially-designed, closed computer network to simulate cyber-attacks without jeopardizing real world networks. Simultaneously, organizational leaders and managers participated in a "table top exercise," dicussing prevention, response and information sharing. Combining both technical and leadership tracks is unique among cybersecurity exercises, Esquibel said. Maymi noted that the institute will work with the participants to publish a report describing the methodology, results, and possible improvement so that other cities may replicate or build upon the exercise.
The Army Cyber Institute will publish videos of each talk on their YouTube channel in late October. Other speakers included:
Bernard Skoch, a retired Air Force general, discussed his experience with CyberPatriot, a youth cyber education program created to inspire middle school and high school students to careers in science, technology, engineering, and math. "Waiting until students are in high school to get them interested in STEM is too late, he said.
Alan Silberberg, founder and CEO of Digijacks, a cybersecurity firm, discussed the need to improve cybersecurity in space. Several countries have developed methods for satellite hacking, a threat to national security and industry.
Mike Walker, a program manager at the Defense Advanced Research Projects Agency, spoke about the Cyber Grand Challenge, a DARPA competition that challenged research teams to develop autonomous computer systems.
Eric Rickard, a vice president and leader of Booz Allen Hamilton's Strategic Innovation Group, likened cybersecurity to judo, using specific precepts to understand and defeat an opponent.
Paulo Shakarian, director of Arizona State University's Cyber-Socio Intelligent System Laboratory, described how intelligence analysis can be augmented by gathering data from malicious hacker communities and marketplaces and using advanced computational techniques.
Santiago Torres-Arias described his research on 'PolyPassWordHasher,' a new approach to password hashing that invited the audience to rethink complex passwords.
Micah Bushouse, a US Army major, described his research with Chief Warrant Officer 3 Joseph Babesh to automate the multitude of cyber defense systems, currently a challenge to offensive cyber operators.
Contact the Army Cyber Institute at West Point via contact.cyber@usma.edu for information on the upcoming CyCon U.S. International Conference on Cyber Conflict, Oct. 21-23 in Washington D.C. (http://aci.cvent.com/cycon_us); the Cyber Defense Review (http://www.cyberdefensereview.org/); future Cyber Talks events, or general inquiries. Follow the Army Cyber Institute on Twitter: @ArmyCyberInst.
-30-
Related Links:
CyCon U.S. International Conference on Cyber Conflict, Oct. 21-23, Washington D.C.




Social Sharing